🧠 Introduction to XWORM V 3.0 Cracked
XWORM V 3.0 Cracked refers to a modified or illegally distributed version of a Remote Access Trojan (RAT) built on the .NET framework. These cracked variants are often shared on underground platforms, making advanced malware accessible to a wider audience, including inexperienced users.
Unlike original builds, cracked versions are frequently repackaged with hidden payloads or backdoors. This means they can pose risks not only to victims but also to the individuals attempting to use them.
⚠️ This article is strictly for educational and cybersecurity awareness purposes only.
🔍 Evolution of XWORM Malware
📈 From Early Versions to Cracked Variants
XWORM V 3.0 Cracked represents a stage where malware became more accessible and dangerous:
🔹 Improved Stability
Compared to earlier builds, this version operates more reliably, allowing attackers to maintain long-term access without crashes.
🔹 Enhanced Stealth
It uses obfuscation and memory-based execution techniques to reduce detection by antivirus tools.
🔹 Wider Accessibility
Cracked distribution lowers the barrier to entry, enabling more users to deploy such tools, increasing overall cyber threats.
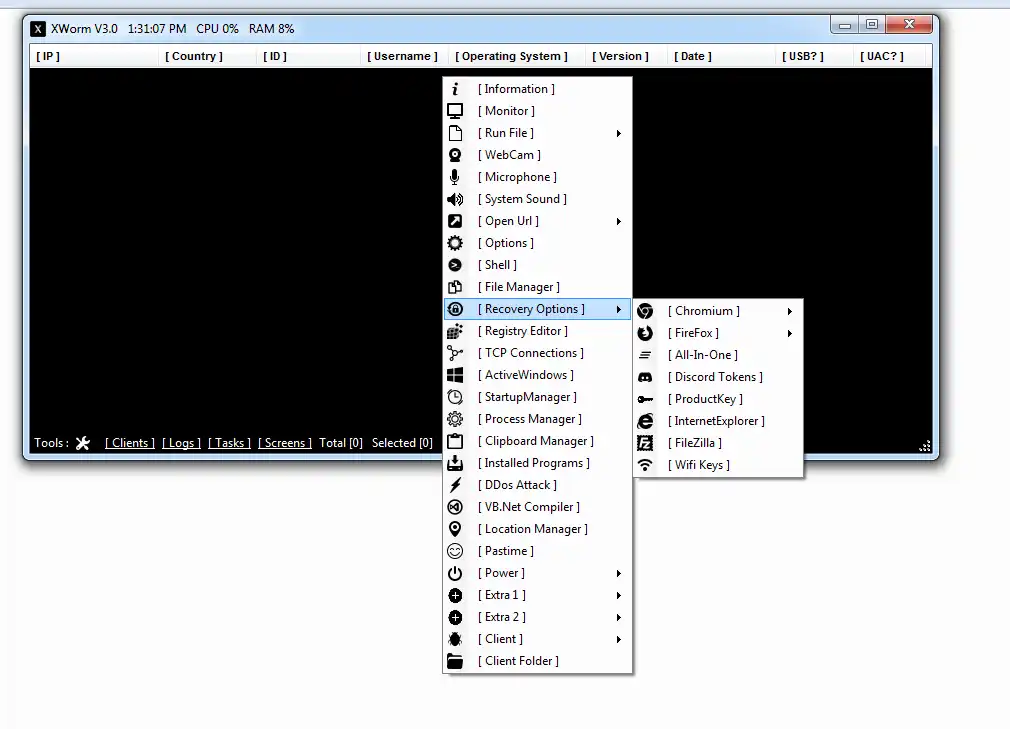
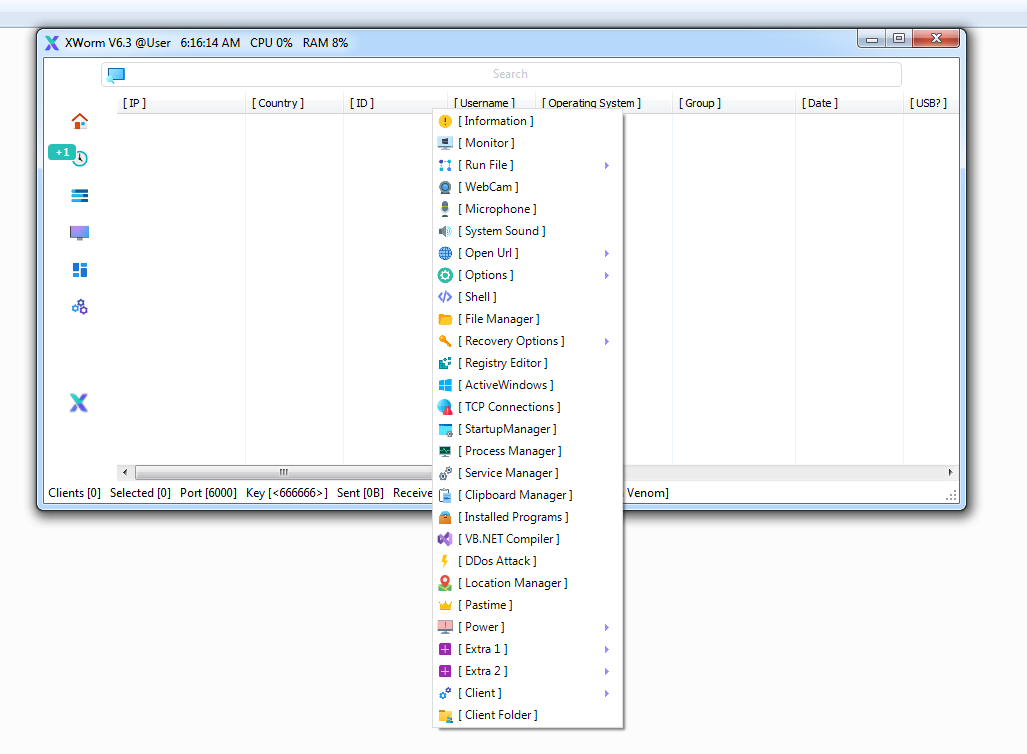
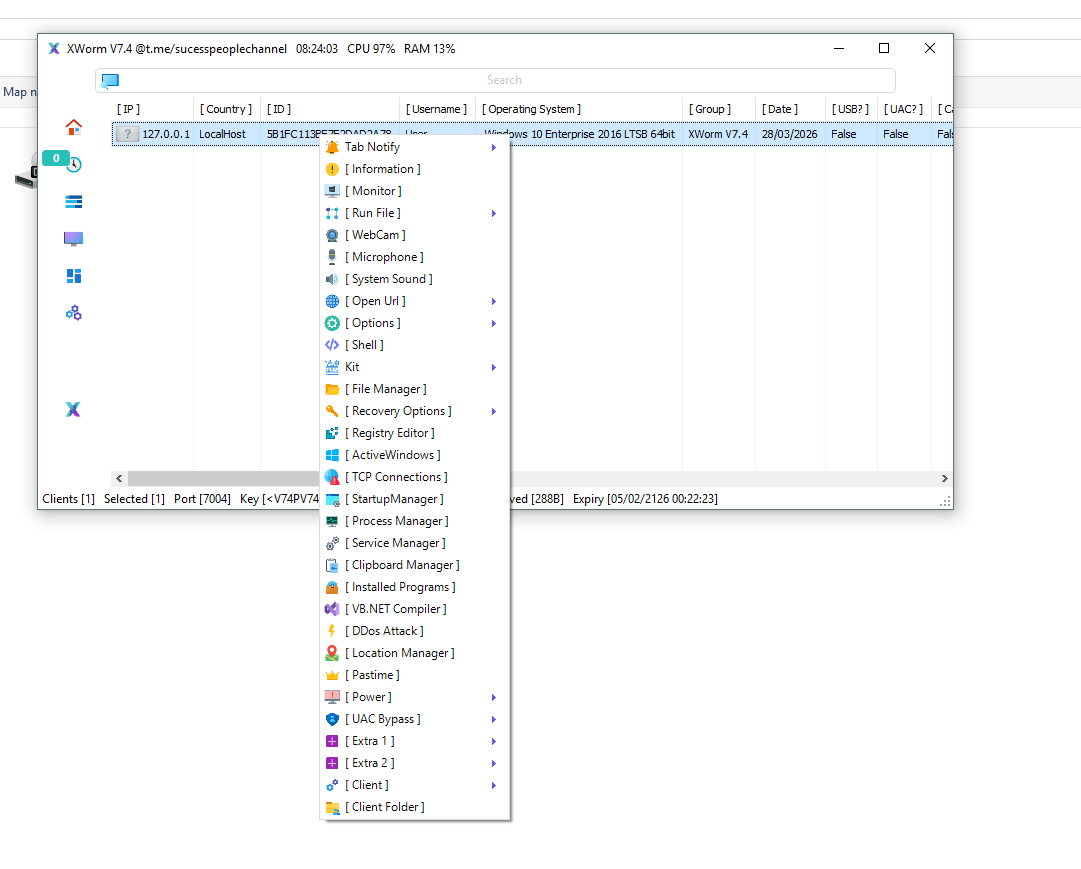
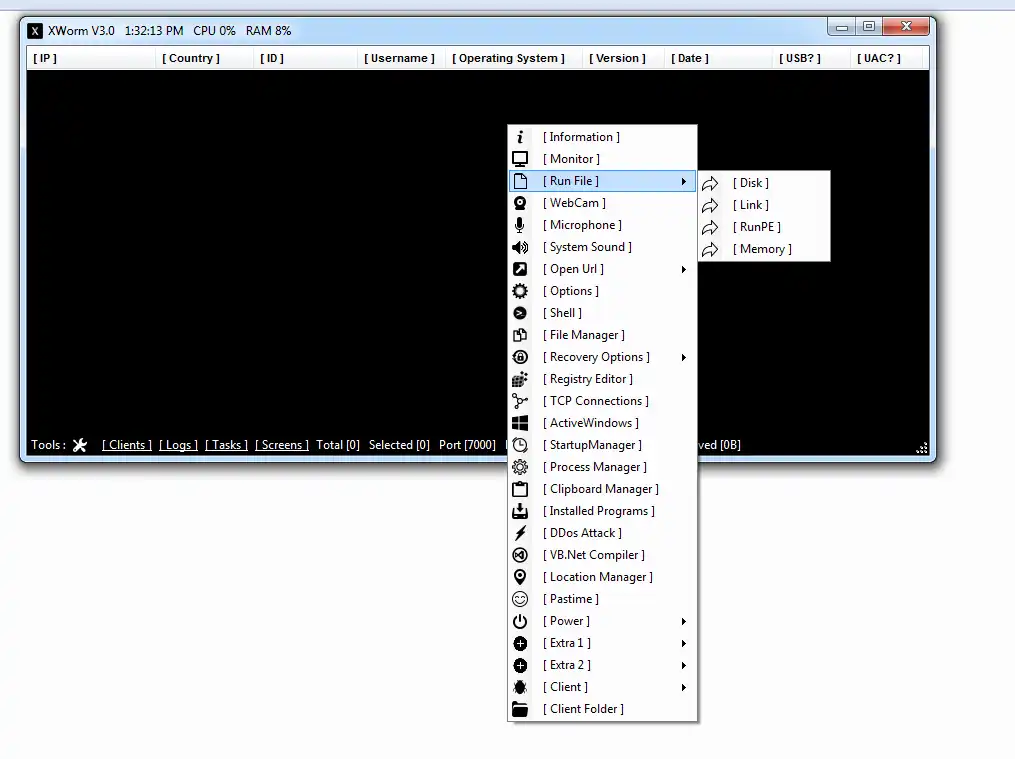
⚙️ Core Features of XWORM V 3.0 Cracked
🛠️ Advanced Capabilities Explained
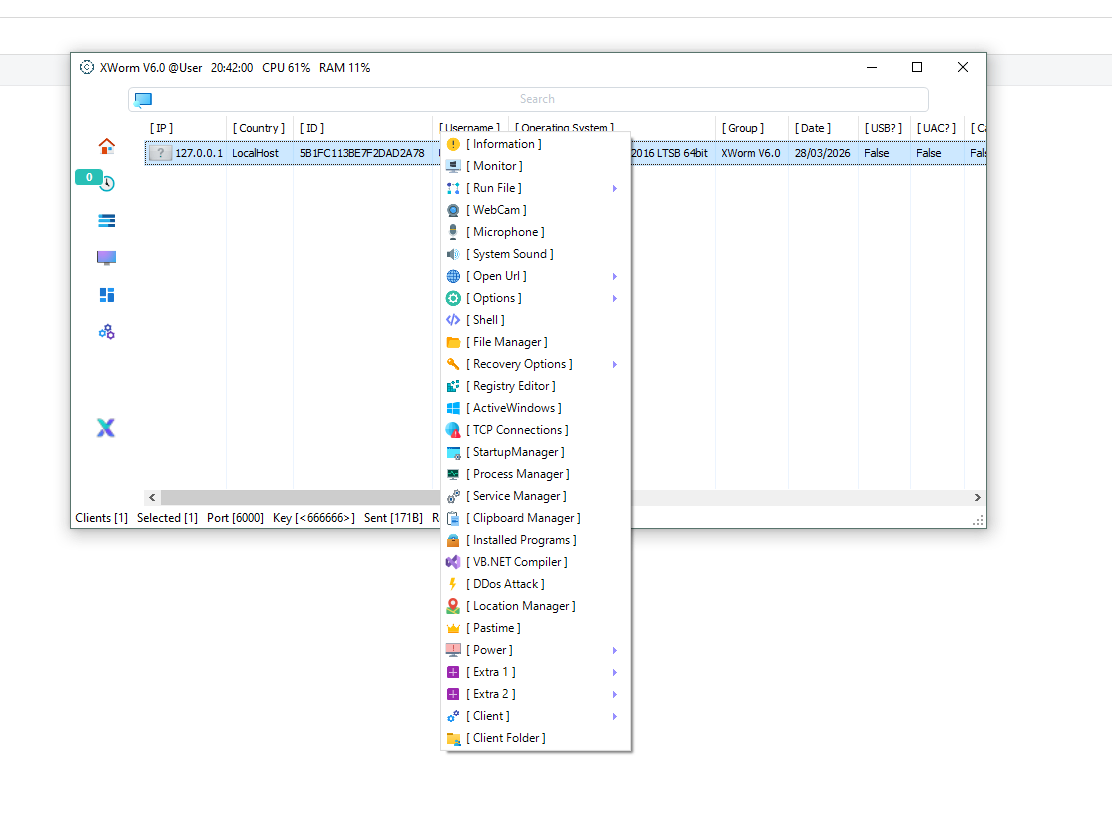
🔹 🖥️ Remote System Control
XWORM V 3.0 Cracked allows full remote access to infected machines. Attackers can execute commands, manage files, and control system operations in real time.
🔹 📂 File Management System
It enables browsing directories, uploading malicious files, downloading sensitive data, and deleting important system files.
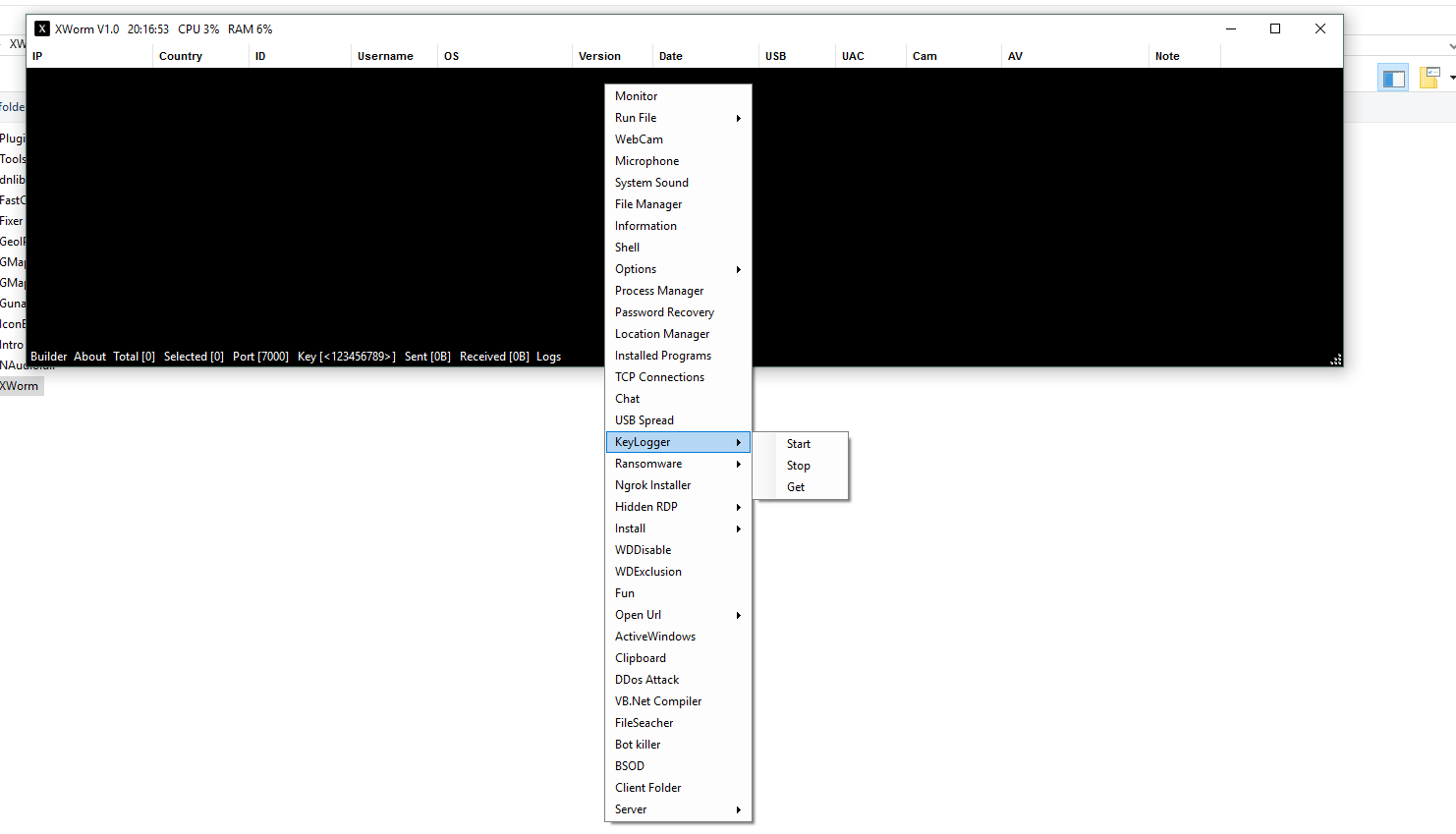
🔹 ⌨️ Keylogging System
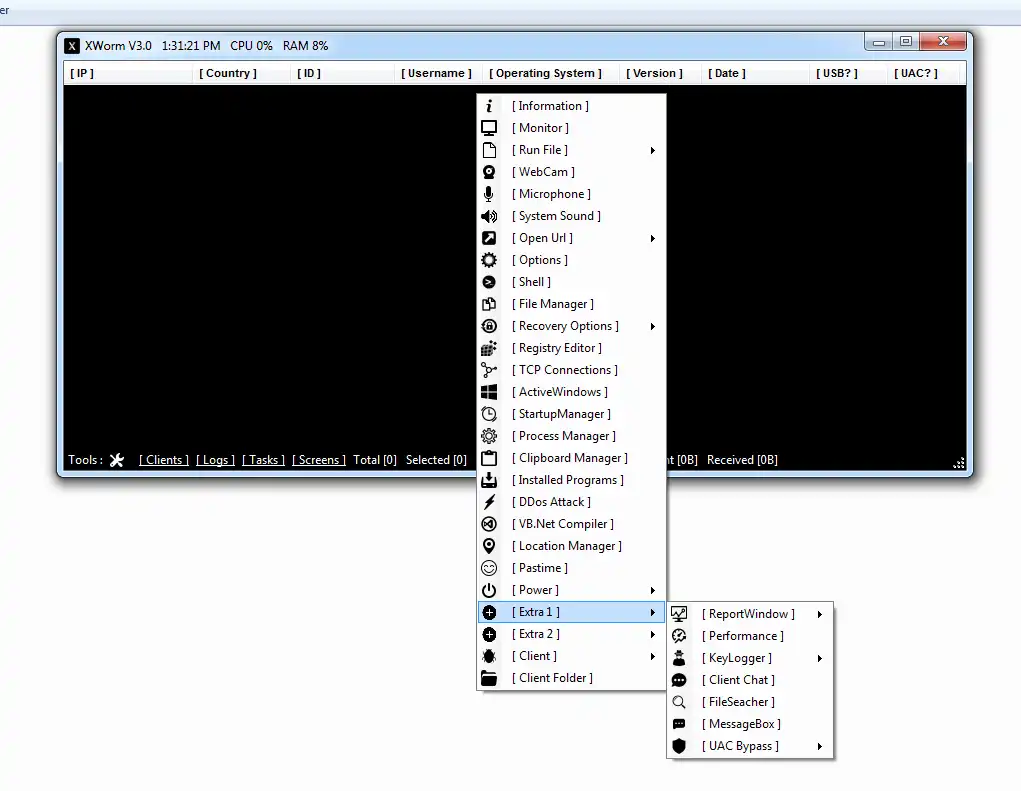
The malware records keystrokes continuously, capturing passwords, private messages, and other sensitive information.
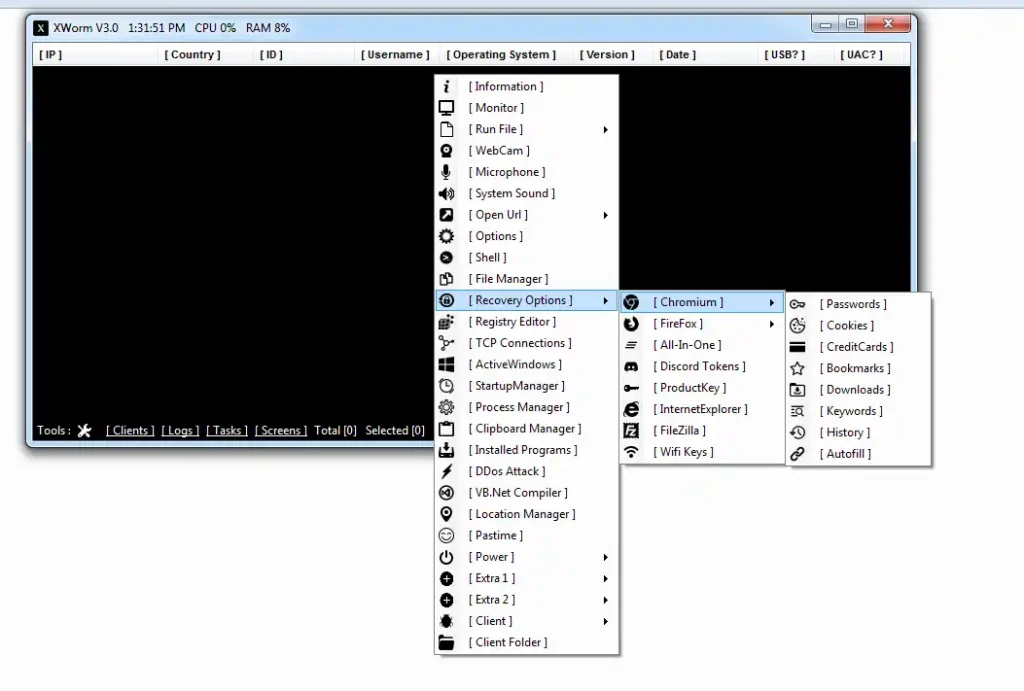
🔹 🔑 Credential Theft Module
It can extract saved credentials from browsers and applications, increasing the risk of account compromise and financial loss.
🔹 📸 Screen Monitoring & Capture
Attackers can take screenshots or monitor the victim’s screen live, allowing full visibility into user activity.
🔹 🔄 Persistence Mechanism
The malware embeds itself into startup processes or system registry entries to maintain long-term access.
🔹 ⚡ Remote Command Execution
Attackers can run system-level commands remotely, giving them deep control over the infected machine.
🔹 🌐 Command & Control (C2) Communication
Maintains a connection with a remote server to receive commands and send stolen data.
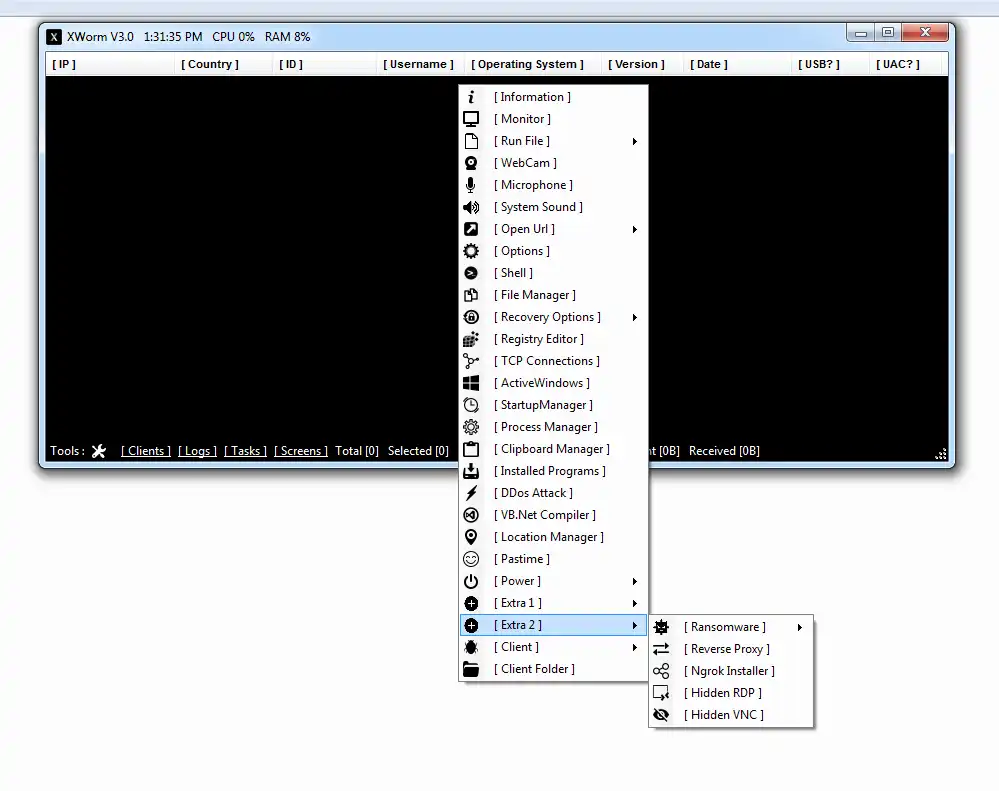
🔹 🧩 Payload Delivery System
It can download and execute additional malware, including spyware or ransomware.
🔹 🕵️ Anti-Analysis Techniques
Includes mechanisms to detect virtual machines or sandbox environments, helping it avoid analysis.
🔹 ⚠️ Hidden Risks in Cracked Versions
Cracked builds may contain extra malicious code, backdoors, or spyware added by third parties, making them even more dangerous.
⚙️ How XWORM V 3.0 Cracked Works
📥 Infection Methods
🔹 Phishing Emails
Malicious attachments disguised as legitimate documents trick users into executing the malware.
🔹 Cracked Software Downloads
Pirated tools often carry hidden malware payloads, making them a major infection source.
🔹 Malicious Websites
Visiting compromised sites can trigger automatic downloads or exploit vulnerabilities.
🔗 Execution Lifecycle
- User opens a malicious file
- The malware executes silently in the background
- XWORM installs itself into system directories
- Persistence is established via registry/startup
- It connects to a Command & Control server
- The attacker gains remote access
🧪 Post-Exploitation Activities
🔹 Data Exfiltration
Sensitive information is collected and transmitted to the attacker.
🔹 Continuous Monitoring
User activity, keystrokes, and screen actions are tracked.
🔹 Additional Malware Deployment
Attackers can expand control by installing more malicious tools.
🔹 Ransomware Risk
Files may be encrypted, and victims may be asked to pay a ransom.
🛠️ Technical Breakdown
| 🔧 Component | 📊 Details |
|---|---|
| Malware Type | Remote Access Trojan (RAT) |
| Language | .NET |
| Persistence | Registry / Startup |
| Communication | Encrypted TCP (C2) |
| Execution | Multi-stage payload |
| Detection Evasion | Obfuscation / Anti-VM |
⚠️ Indicators of Compromise (IOCs)
🚩 Warning Signs
🔹 🐢 System Slowdown
Unexpected lag due to hidden malicious processes.
🔹 🔍 Unknown Processes
Suspicious background applications running without user knowledge.
🔹 🌐 Unusual Network Activity
Frequent communication with unknown servers.
🔹 ❌ Disabled Security Tools
Antivirus or firewall being turned off automatically.
🔹 🔐 Unauthorized Account Access
Signs of compromised credentials.
🔐 Protection & Prevention Strategies
🛡️ Best Practices
🔹 🚫 Avoid Cracked Software
Using tools like XWORM V 3.0 Cracked significantly increases the risk of infection.
🔹 📧 Email Awareness
Do not open suspicious attachments or click unknown links.
🔹 🧰 Use Updated Security Tools
Modern antivirus and endpoint protection solutions can detect threats early.
🔹 🔄 Regular Updates
Keep systems patched to close security vulnerabilities.
🔹 🔒 Monitor Network Traffic
Detect unusual activity early to prevent damage.
Download XWORM V 3.0 Cracked
🧠 Conclusion
XWORM V 3.0 Cracked highlights the increasing accessibility and danger of modern malware. While it offers powerful capabilities for attackers, it also introduces serious risks due to hidden payloads and unpredictable behavior in cracked versions.
Awareness and proactive security measures remain the most effective defense against such threats.
❓ Frequently Asked Questions (FAQ)
❓ What is XWORM V 3.0 Cracked?
It is a modified version of a Remote Access Trojan that provides unauthorized remote control over systems.
❓ Is XWORM V 3.0 Cracked safe?
No, it is unsafe and may contain hidden malware that can harm both users and victims.
❓ How does it spread?
It spreads via phishing emails, malicious downloads, and cracked software.
❓ Can antivirus detect it?
Yes, but advanced obfuscation techniques may help it evade basic detection.
❓ What should I do if infected?
Disconnect from the internet, run a full antivirus scan, and consider reinstalling your system.