malware analysis
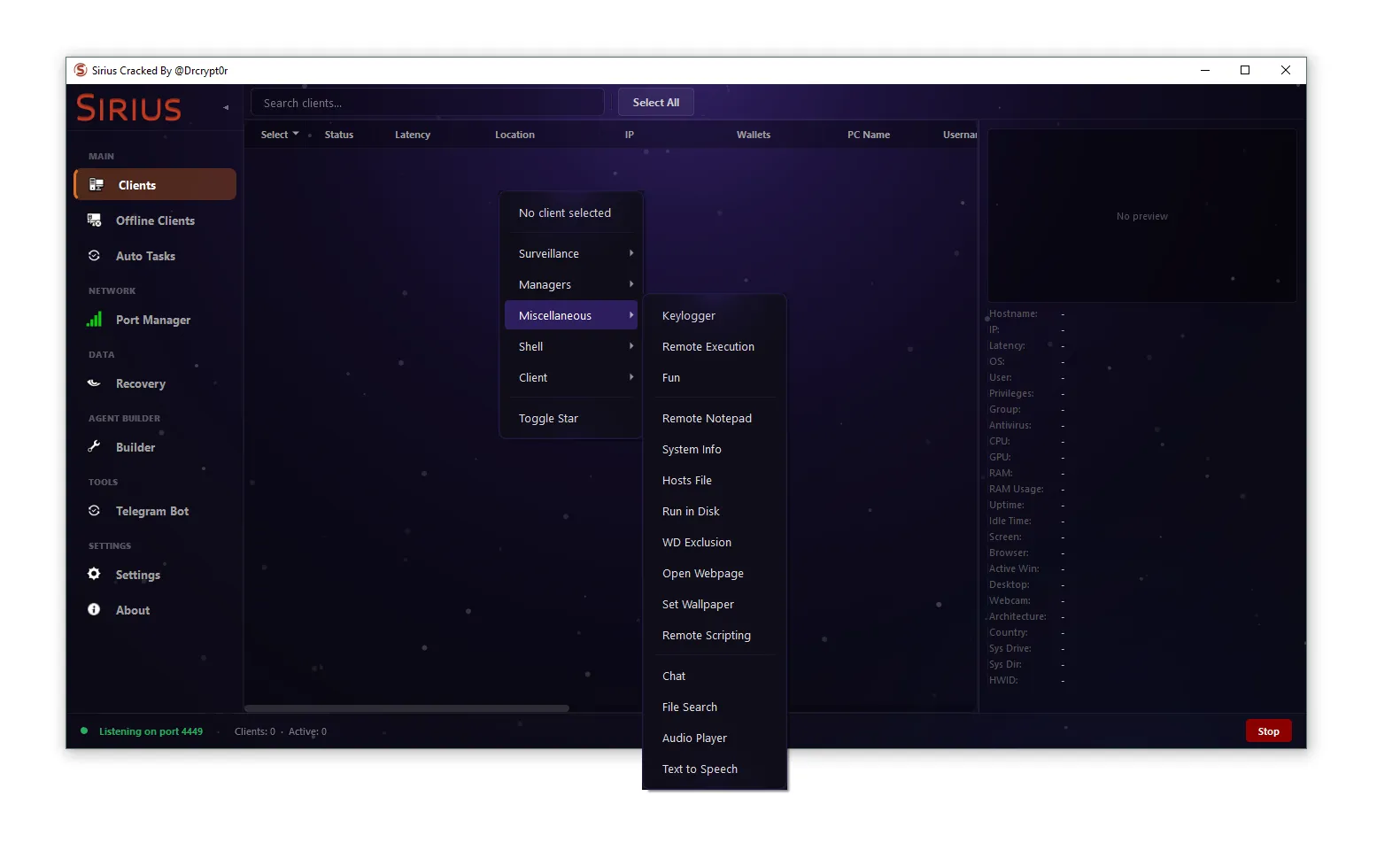
SiriusQT RAT 2026
The rise of advanced cyber threats has made Remote Access Trojans (RATs) one of the most dangerous tools in modern cybercrime. Among them, SiriusQT...
Abko RAT 2026
🛡️ Abko RAT 2026: Complete Cybersecurity Analysis & Defense Guide In today’s rapidly evolving cybersecurity landscape, Remote Access Trojans (RATs) have become one of...
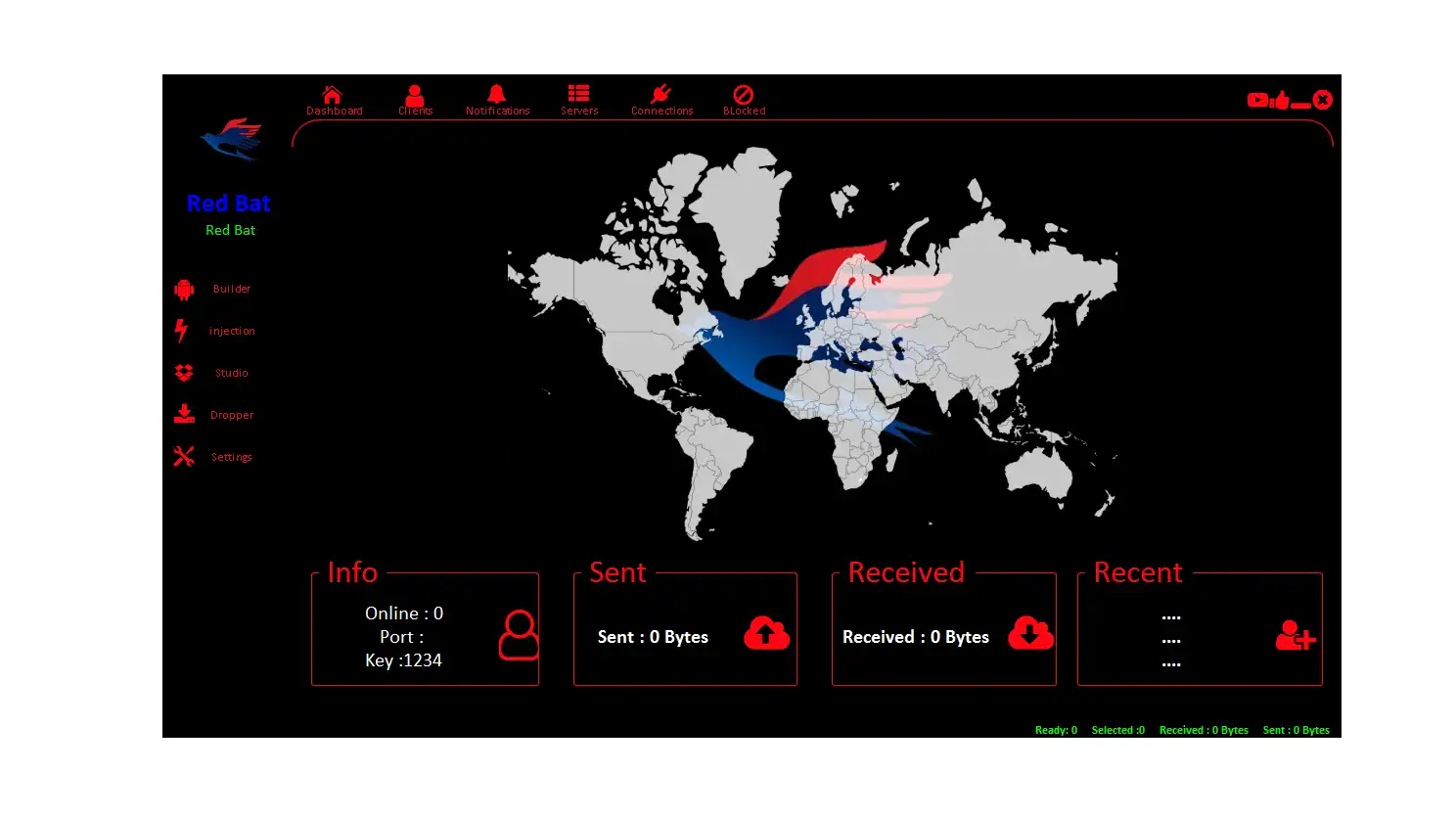
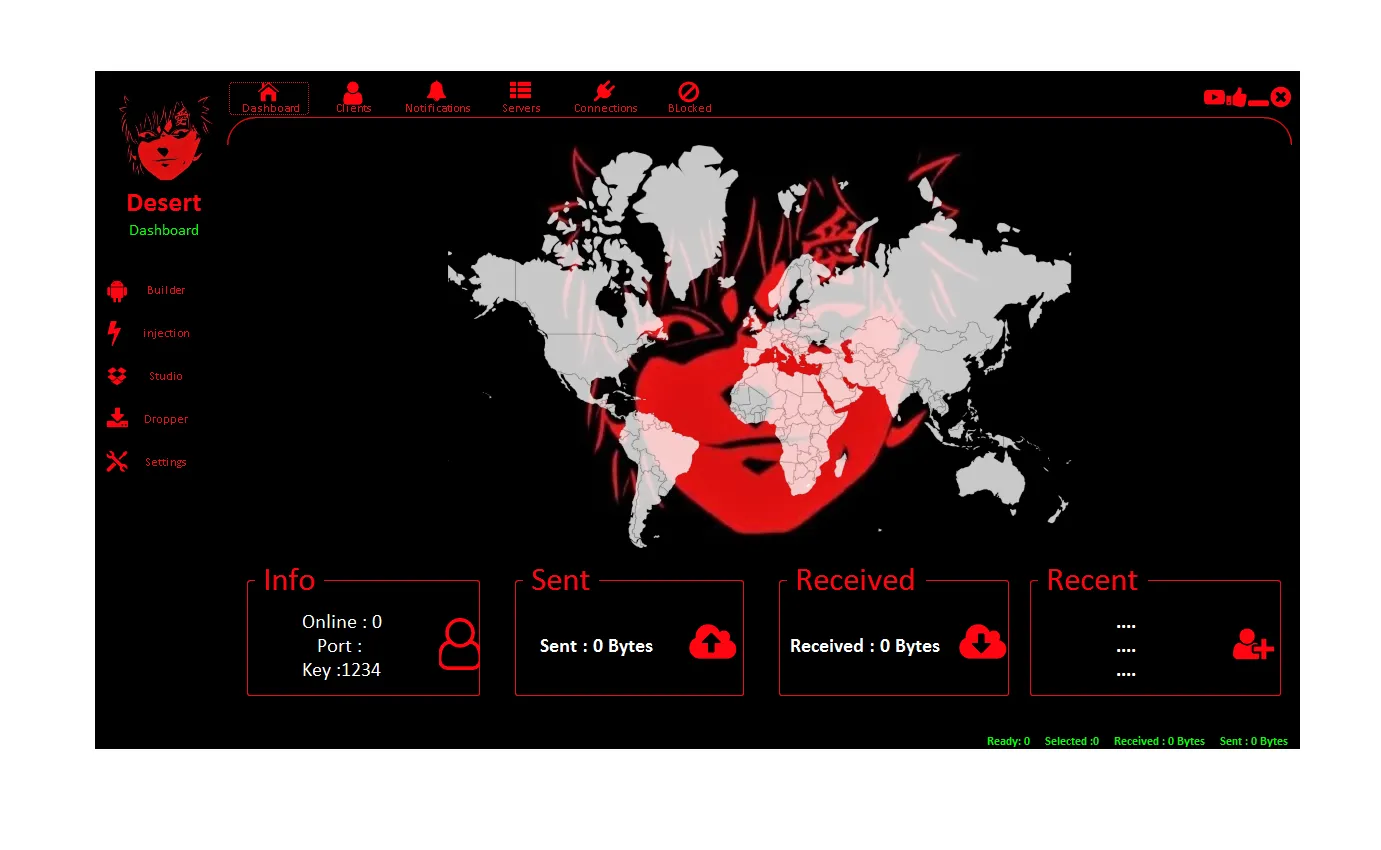
RedBat RAT 2026
📱 Introduction RedBat RAT 2026 The modern mobile ecosystem is facing an unprecedented rise in Android malware, particularly Remote Access Trojans (RATs) like RedBat...
VIP RAT V 2026
🔥 VIP RAT V 2026 – In-Depth Guide to Android Remote Administration Tools, Risks & Protection As mobile technology continues to evolve, Android devices...
Medusa RAT 2026
🔥 Medusa RAT 2026: Complete Android Malware Analysis, Features, and Security Risks 📱 Introduction: Understanding Medusa RAT 2026 Medusa RAT 2026 is a next-generation...
S400 RAT 2026
S400 RAT 2026 (Cracked) – Complete Malware Analysis, Features & Security Risks 🧠 Introduction S400 RAT 2026 S400 RAT 2026 (Cracked) is a highly...
Icarus Evil Worm Cracked 2026
🧠 Introduction The cybersecurity landscape in 2026 has taken a dangerous turn with the rise of Icarus Evil Worm Cracked 2026. Once a premium...
Eclipse RAT 2026 Cracked
🧠 Introduction The rise of Eclipse RAT 2026 Cracked has become a major concern in the cybersecurity world. Originally developed as a premium remote...
XWorm V5.7 Chinese Edition Cracked
🧲 🔍 Introduction to XWorm V5.7 Chinese Edition Cracked XWorm V5.7 Chinese Edition Cracked is an unofficial, modified, and often illegally distributed version of...
XWORM V 3.0 Cracked
🧠 Introduction to XWORM V 3.0 Cracked XWORM V 3.0 Cracked refers to a modified or illegally distributed version of a Remote Access Trojan...