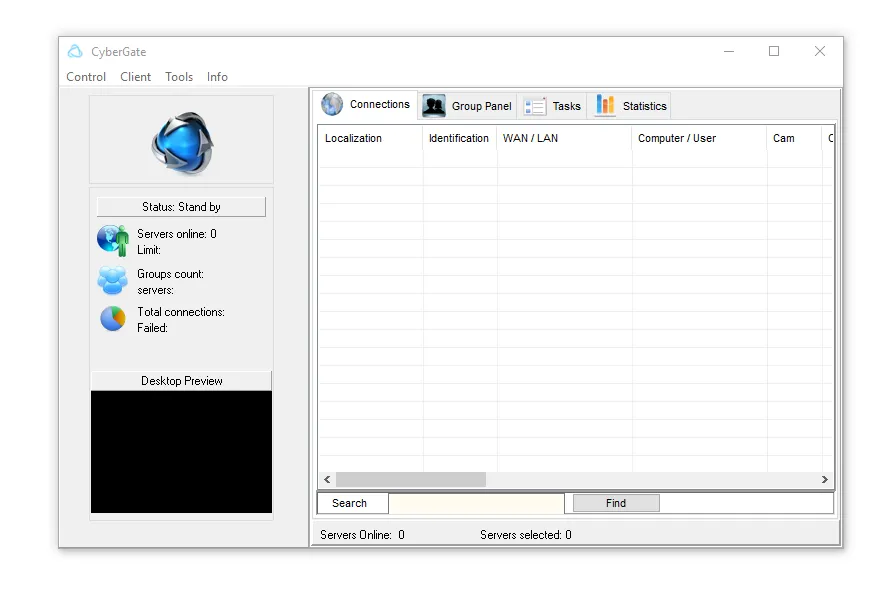
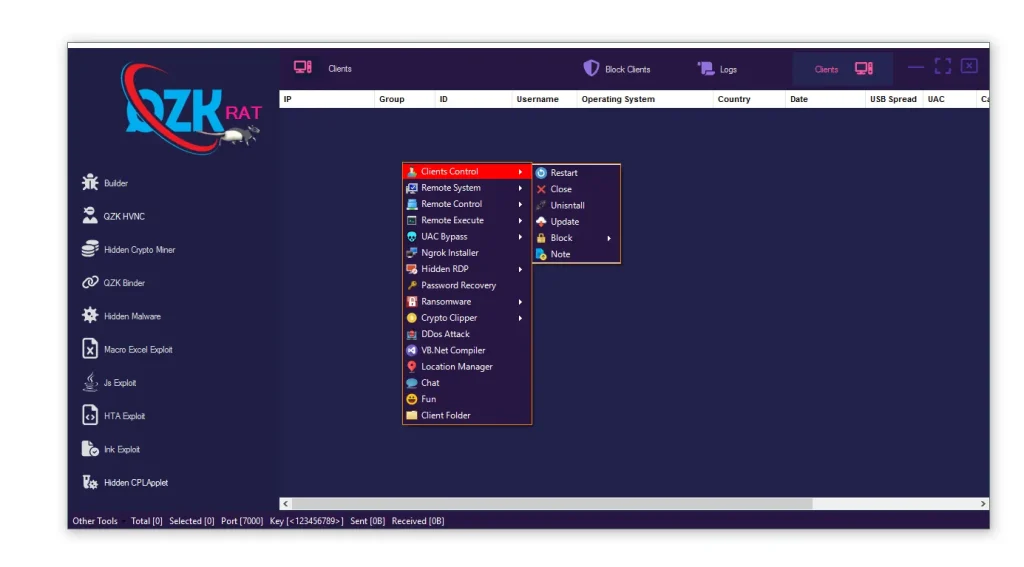
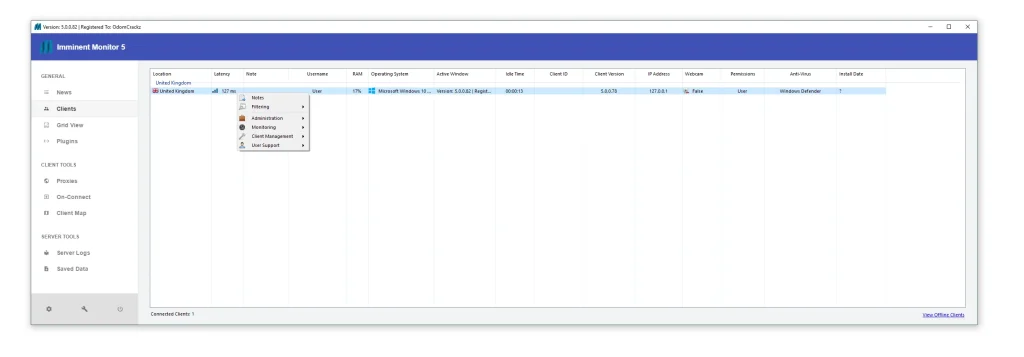
Malware
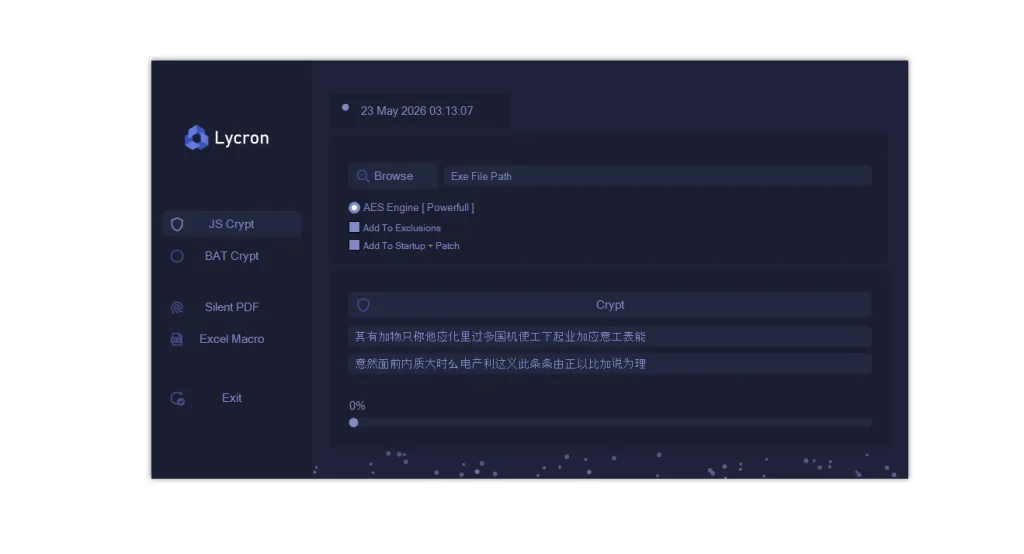
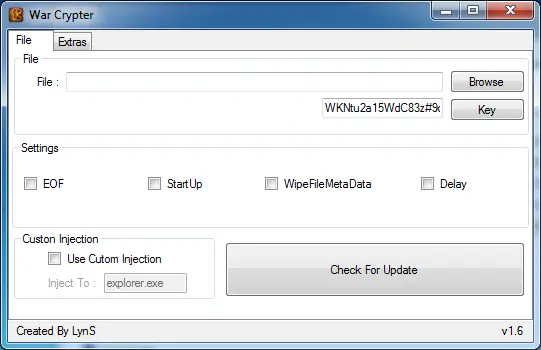
Crypter
Exploiter
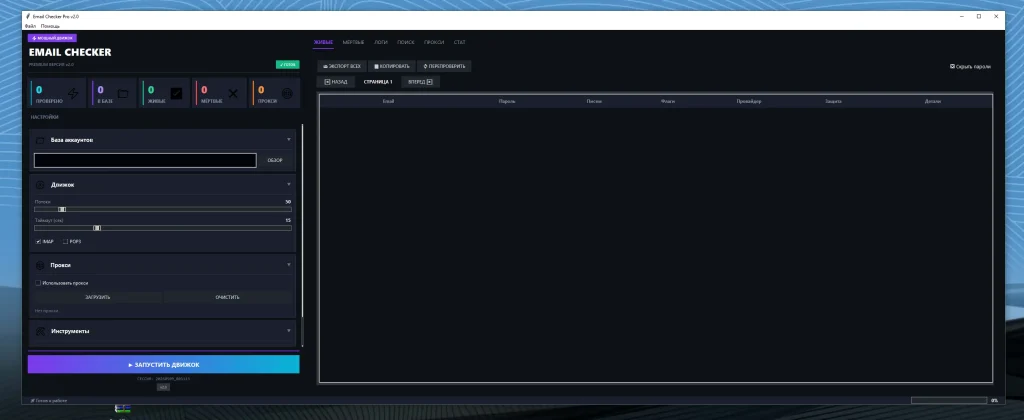
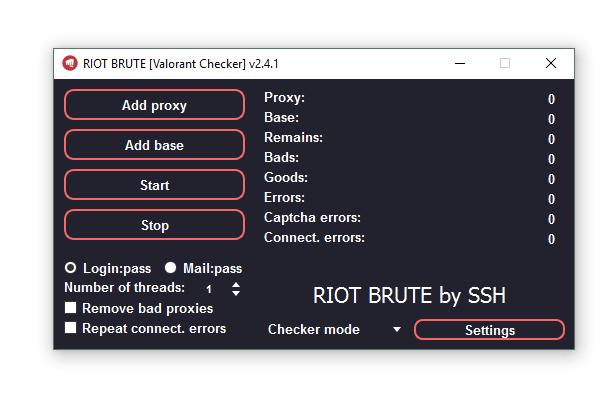
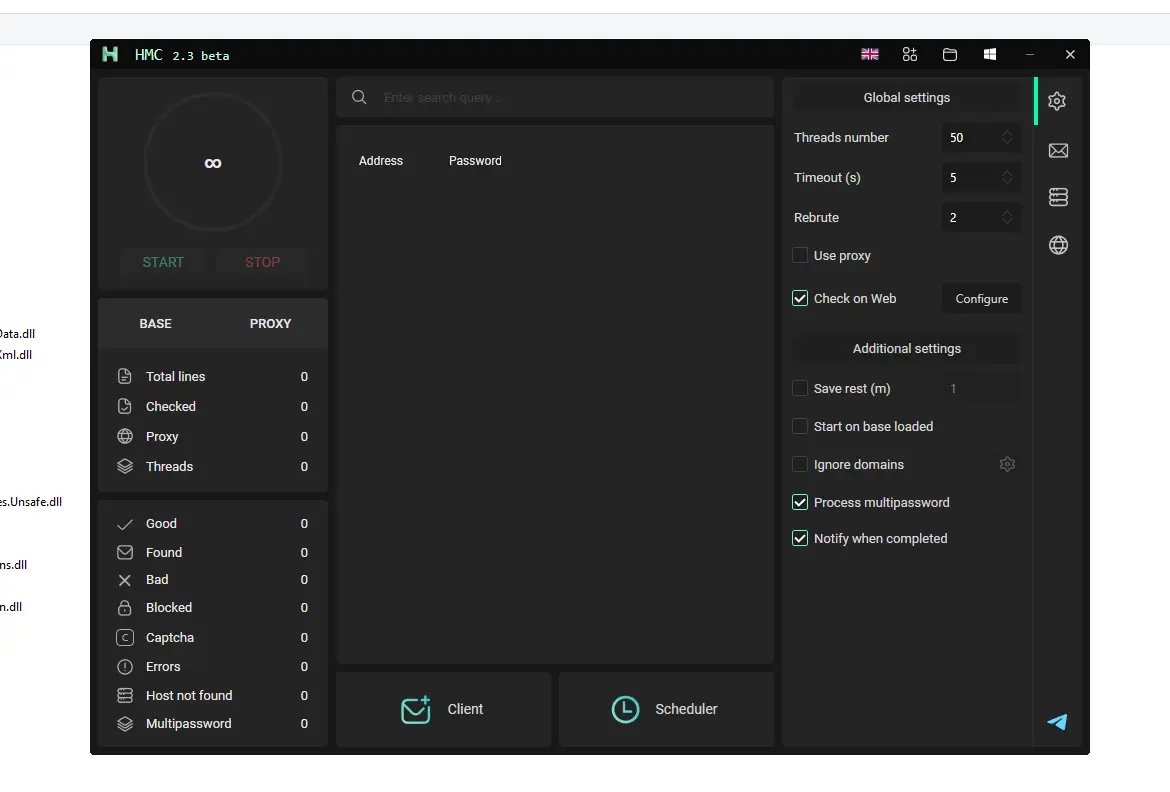
Bruter
Cracked Software
Pentest Tools
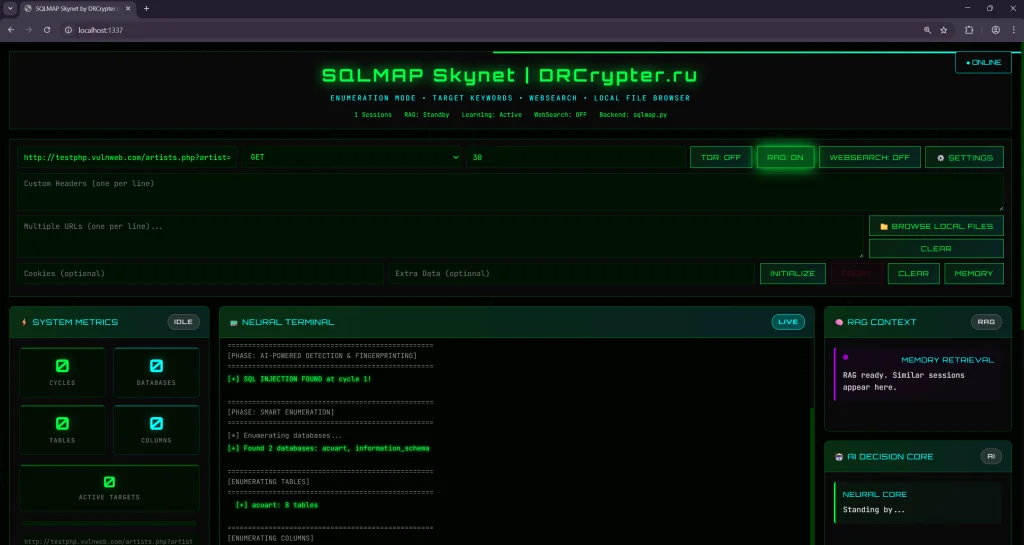
SQLMAP SKYNET Autonomous AI v1.2.0
SQLMAP SKYNET Autonomous AI v1.2.0: A Next-Gen Autonomous SQL Injection Framework In the world of cybersecurity and penetration testing, automation and intelligence are essential. SQLMAP SKYNET Autonomous AI v1.2.0 is…
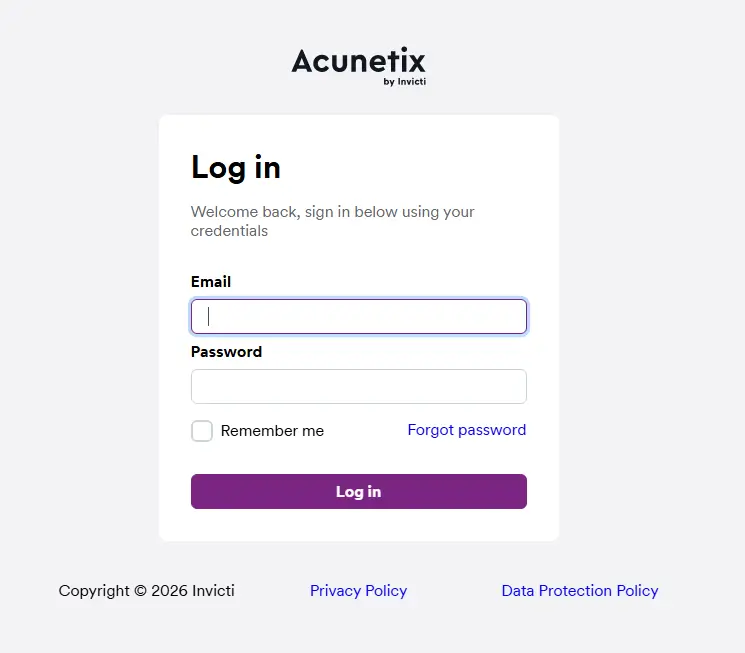
Acunetix Web Vulnerability Scanner V 24.2
Acunetix Web Vulnerability Scanner V 24.2 – Complete Pro Guide (Fast Setup + Tutorial) In today’s digital world, websites and web apps are attacked every day through common security holes…
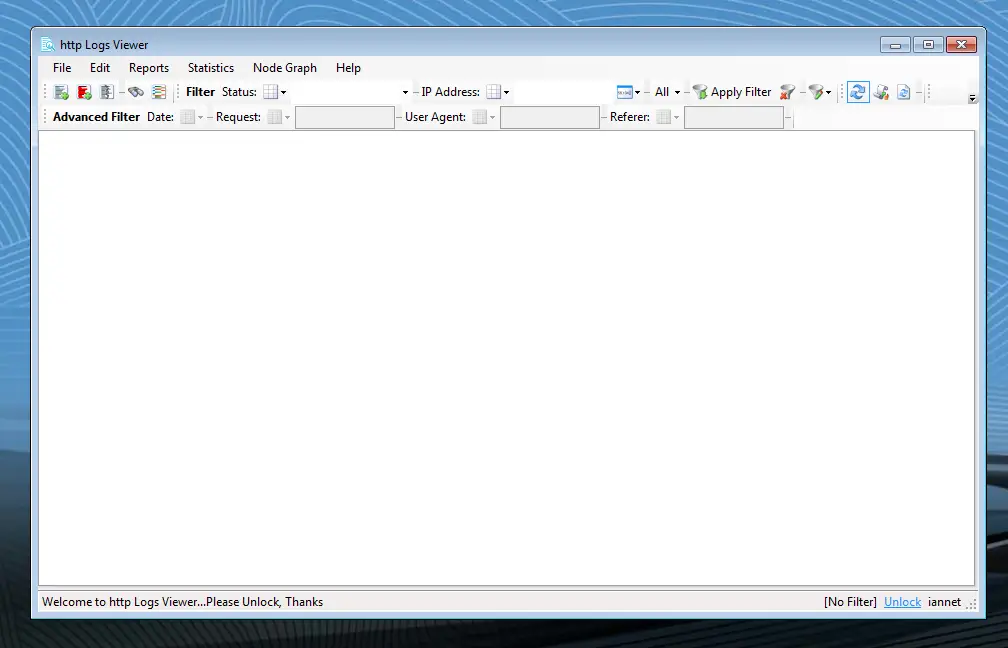
HTTP Logs Viewer 7.0
HTTP Logs Viewer 7.0: Powerful Tool to Analyze Apache, IIS, and Nginx Logs in 2025 HTTP Logs Viewer 7.0: Powerful Tool to Analyze Apache, IIS, and Nginx Logs in 2025…
Proxy TOols
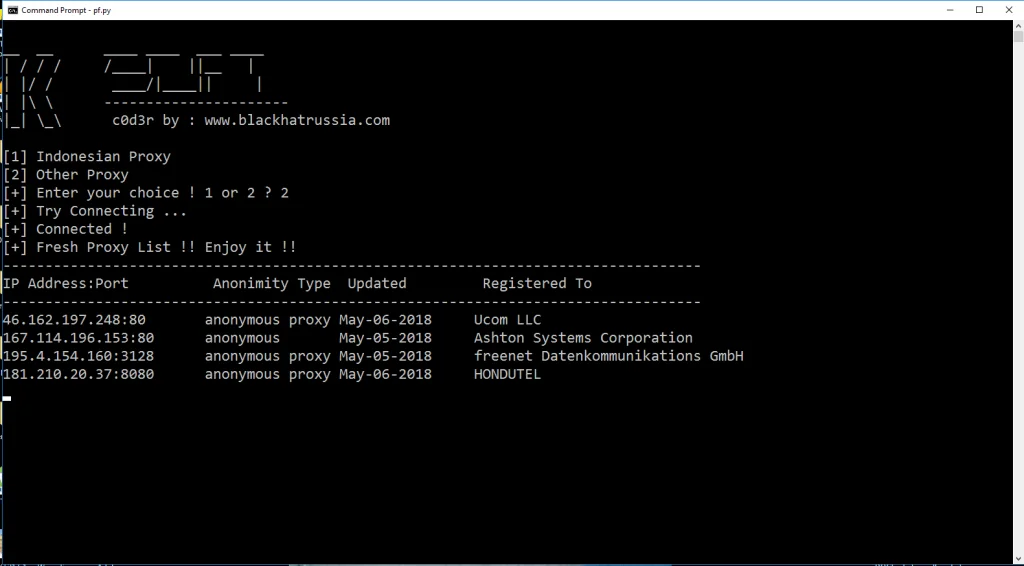
python proxy finder 2025
python proxy finder 2025
NetGhost v1.4
NetGhost v1.4 Proxy scrapper and manager NetGhost v1.4 Proxy scrapper and manager Net Ghost is the ultimate free solution for all your proxy needs. FEATURES
Betternet Vpn Premium Version 4.4.0 Full
Betternet Vpn Premium Version 4.4.0 Full Betternet Vpn Premium Version 4.4.0 Full is a simple but powerful and fully functional proxy software that enables a user to surf the web…
Dns Jumper v2
Dns Jumper v2 DNS jumper is a free utility software that helps you to easily switch from Google to Open Public DNS and other services. It gives you the ability…
Tuorial
Certified Ethical Hacker v10 PDFs Books
Certified Ethical Hacker v10 PDFs Books CEH v10 – Certified Ethical Hacker v10 full PDF is Available for Download now. The worlds most advanced ethical hacking course with 20 of…
Hacking Android 2025
Hacking Android 2025 very useful book for starting hacker with full tools and tutorials
CEH V11 EC-COUNCIL CERTIFIED ETHICAL HACKER ALL MODULES PDF
CEH V11 EC-COUNCIL CERTIFIED ETHICAL HACKER ALL MODULES PDF The world of cybersecurity is a battlefield, with ethical hackers acting as the white knights defending against malicious attackers. If you’ve…
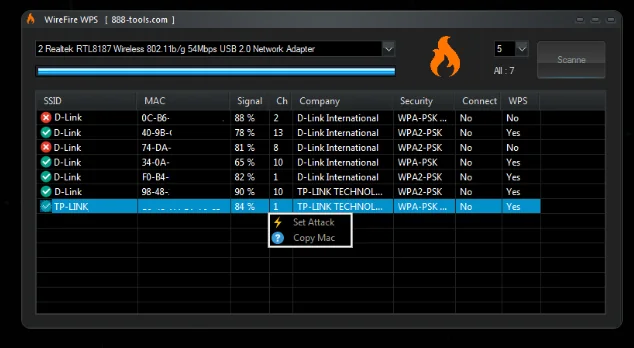
WiFi Hacking for Beginners 2025
WiFi Hacking for Beginners 2025 In this WiFi Hacking for Beginners 2025 book we completely teach you how will start as a beginner without knowledge about penetration testing. The…