cybersecurity threats
XWorm V6.0 Cracked
🚨 XWorm V6.0 Cracked Explained: Complete Features, Builder Plan & Cybersecurity Risks 🧠 Introduction In the rapidly evolving world of cybersecurity, XWorm V6.0 Cracked...
XWorm V6.3 Cracked
🚨 XWorm V6.3 Cracked Explained: Complete Features, Builder Plan & Cybersecurity Risks 🧠 Introduction In today’s evolving cybersecurity landscape, XWorm V6.3 Cracked has emerged...
XWorm V7.4 Cracked
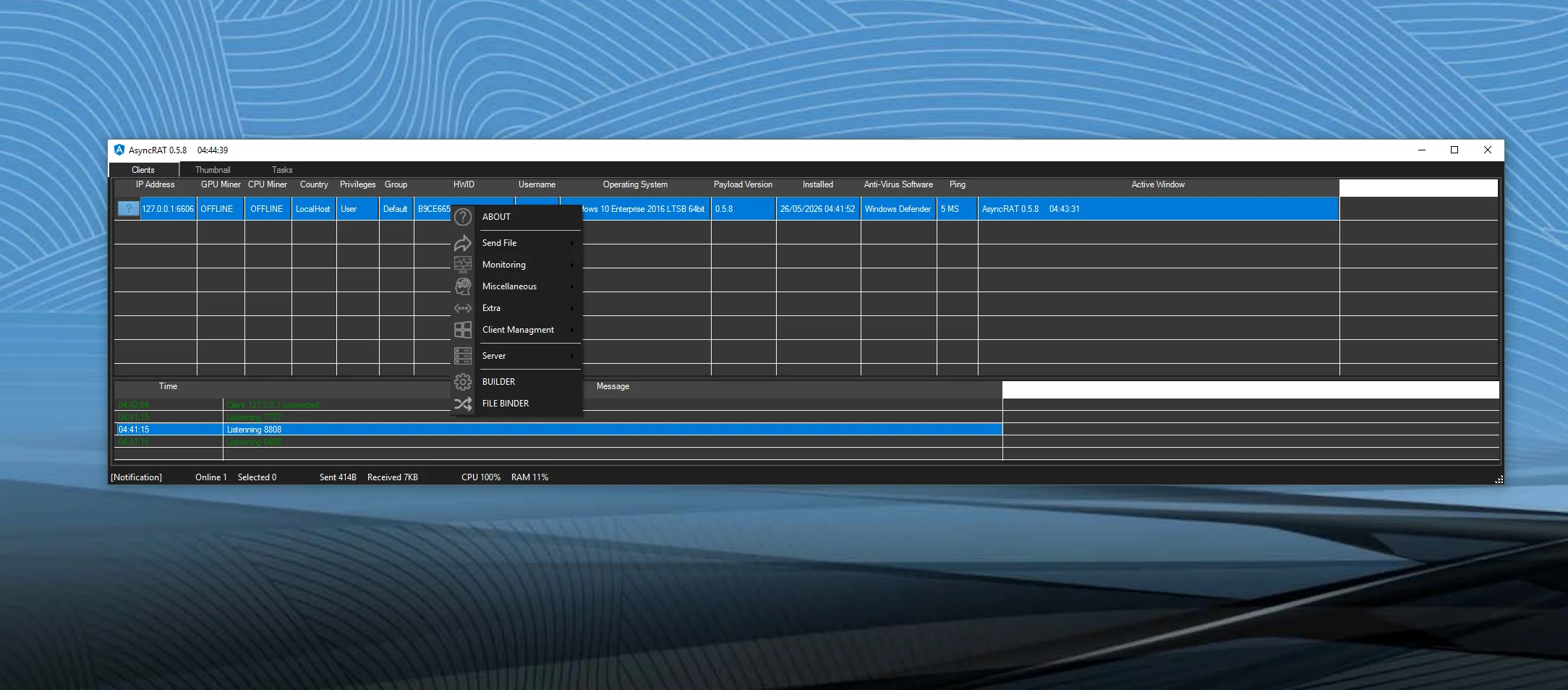
❓ What is XWorm V7.4 Cracked? XWorm V7.4 Cracked refers to an unauthorized modified version of a Remote Access Trojan (RAT) that removes licensing...
Nigger RAT v1.8
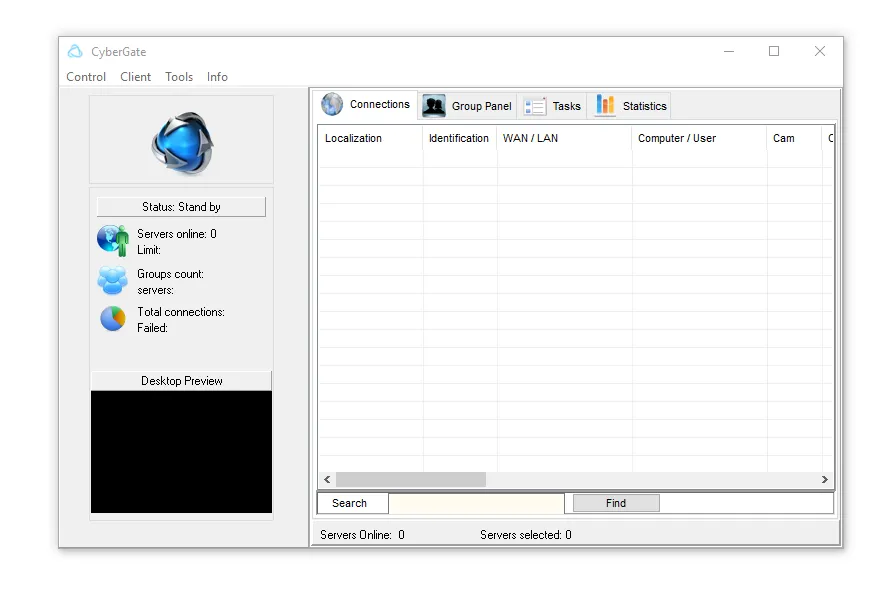
Remote Access Trojans (RATs) remain one of the most dangerous cyber threats today. Nigger RAT v1.8 is a modern evolution of RAT malware designed...
NullRAT 2026
🧠 Introduction to NullRAT 2026 The cybersecurity landscape continues to evolve as attackers develop increasingly sophisticated malware frameworks. One of the threats gaining attention...
Phemedrone Stealer 2026
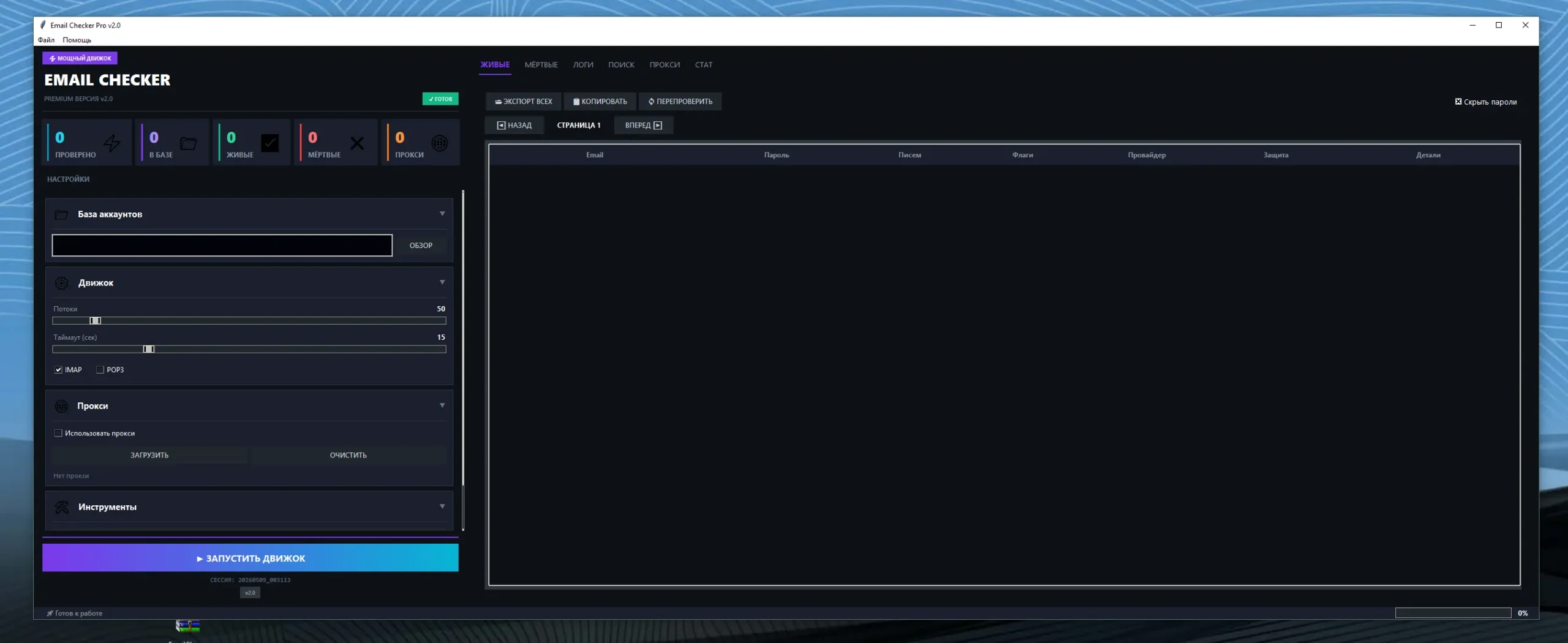
🛡️ Phemedrone Stealer 2026 – Complete Malware Analysis, Features, Architecture & Cybersecurity Risks 🔎 Introduction to Phemedrone Stealer 2026 In recent years, information-stealing malware...
PySilon 2026
🛡️ PySilon 2026 Malware: Complete Technical Analysis of the Python-Based RAT Framework 🔍 Introduction to PySilon 2026 Malware The cybersecurity landscape continues to evolve...
ZsTeal Stealer 2026
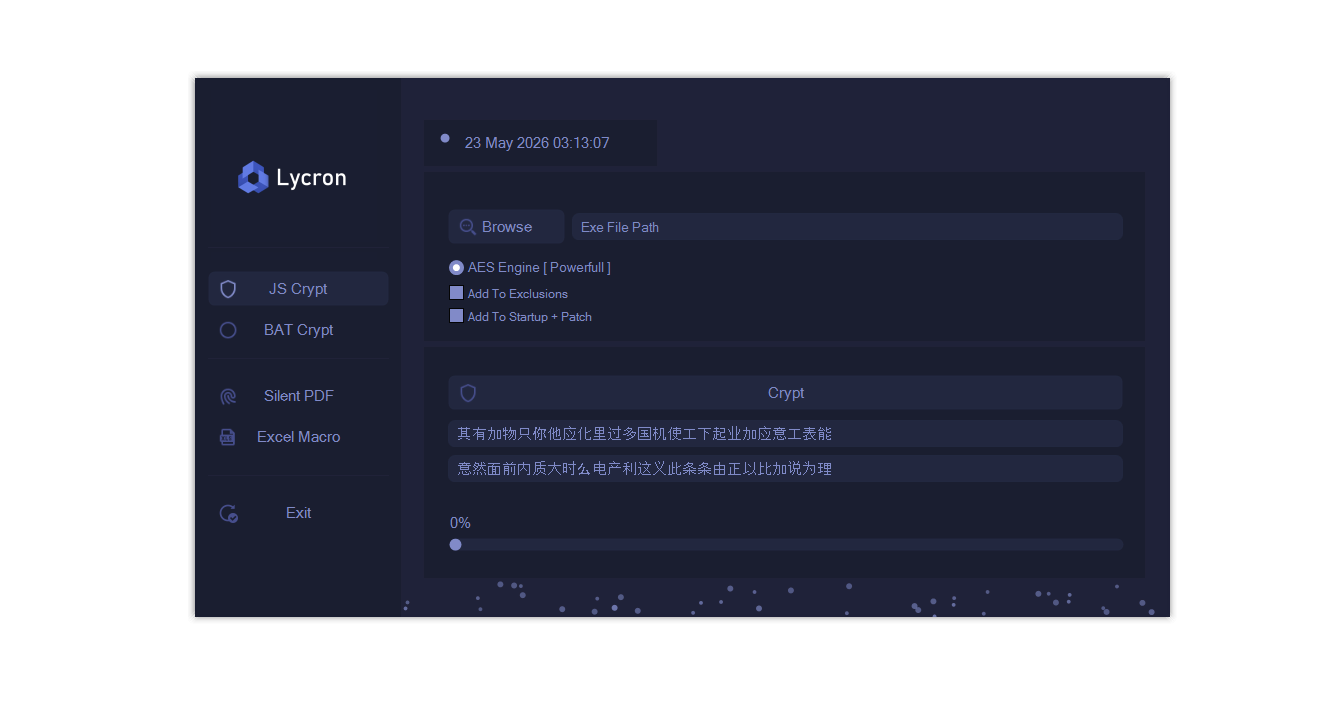
🛡️ ZsTeal Stealer 2026 – Technical Analysis of a Modern Infostealer Malware 🔍 Introduction The cybersecurity landscape continues to evolve as information-stealing malware (infostealers)...
SVCHOST Injector 2026
🧠 Understanding SVCHOST Injector 2026 Attacks in Modern Windows Systems In modern cybersecurity threats, attackers frequently use process injection techniques to hide malicious code...
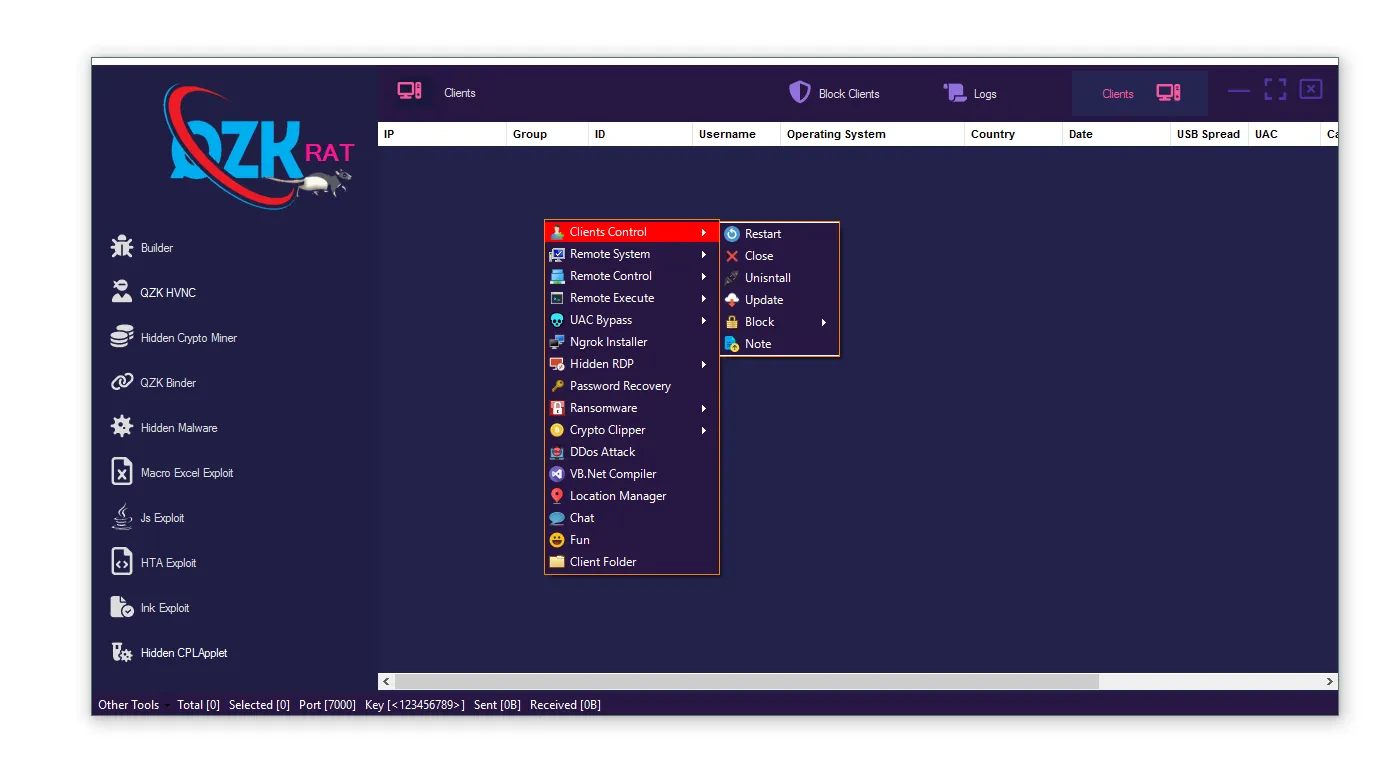
Venom Pro 6.0.9 RAT Cracked
Venom Pro 6.0.9 RAT Cracked The rise of Remote Access Trojans (RATs) has significantly reshaped the modern cyber threat landscape. Among the most discussed...