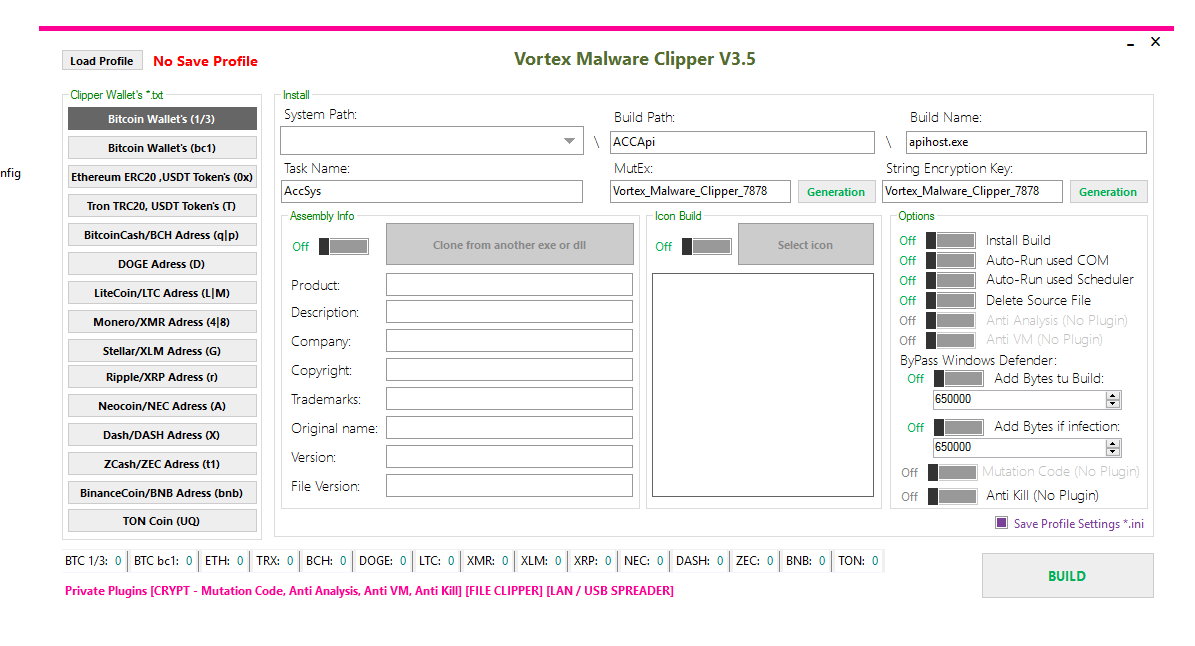
malware analysis
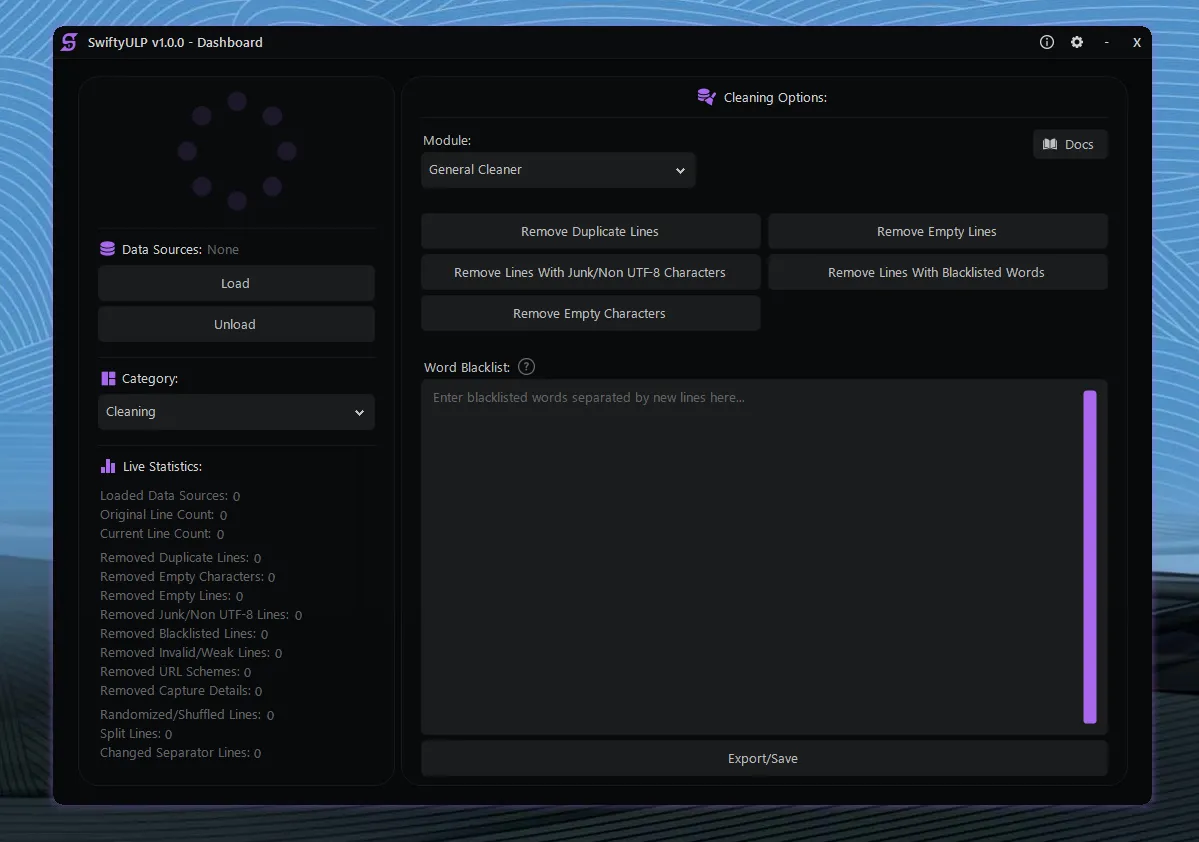
Vortex Malware Clipper V3.5
🛡️ Vortex Malware Clipper V3.5 – Complete Technical Analysis of a Cryptocurrency Clipboard Hijacker 🧠 Introduction to Vortex Malware Clipper V3.5 Cryptocurrency users face...
AVM Stealer 2026
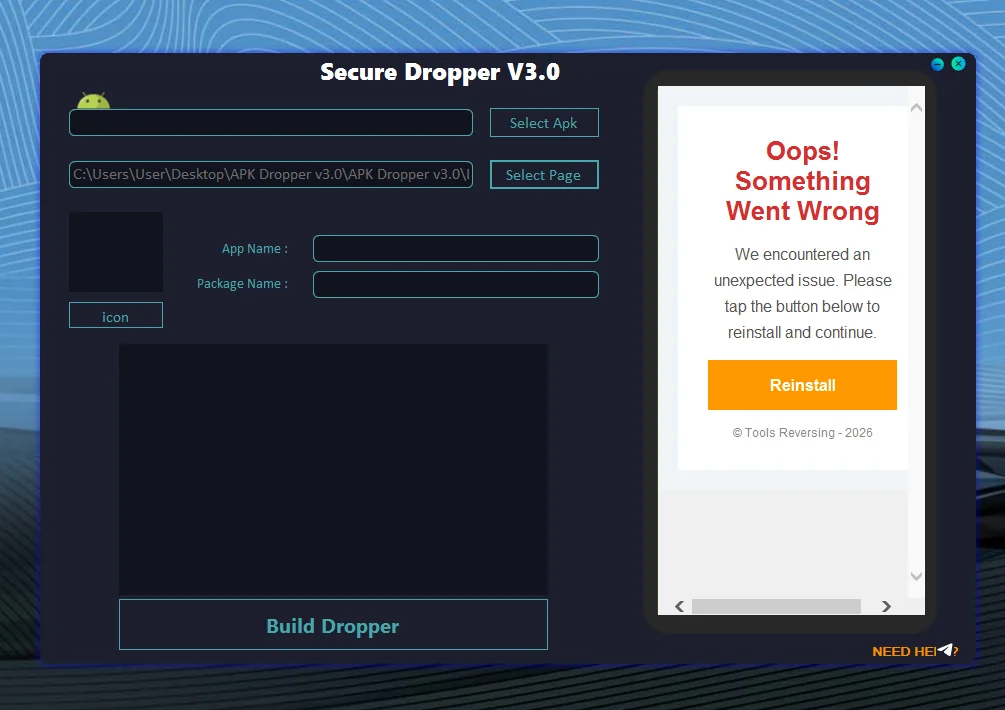
AVM Stealer 2026 – Advanced Infostealer Threat Analysis & Protection Guide Introduction AVM Stealer 2026 is being discussed in cybersecurity circles as a next-generation...
Duplex Spy 2026
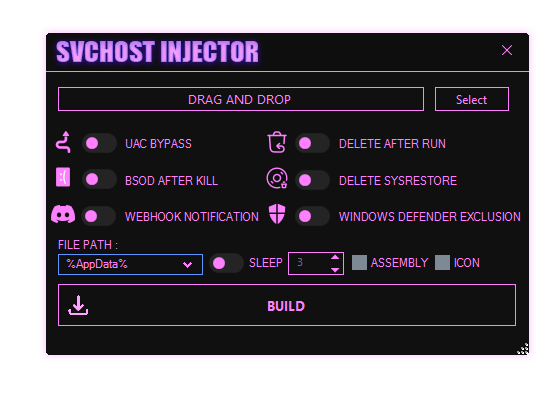
Duplex Spy 2026 – In-Depth Analysis of a Modern Windows RAT for Security Research Overview of Duplex Spy 2026 Duplex Spy 2026 is a...
NeptuneRAT V2.0
NeptuneRAT V2.0: Features and Ethical Considerations NeptuneRAT V2.0 is advertised as a powerful remote administration tool (RAT) explicitly presented for educational and ethical testing...
Doge Rat 2026
Doge Rat 2026 – Technical Analysis, Features, and Cybersecurity Research Overview Introduction to Doge Rat 2026 Doge Rat 2026 is an open-source Remote Access...
Destiny Stealer 2026
Destiny Stealer 2026: Technical Overview, Capabilities, and Cybersecurity Implications Introduction to Destiny Stealer 2026 Destiny Stealer 2026 is a publicly available open-source project hosted...
XWorm RAT v6.5
XWorm RAT v6.5: The Evolving Threat in Cybersecurity Introduction In the ever-evolving landscape of cybersecurity threats, XWorm RAT v6.5 stands out as a sophisticated...