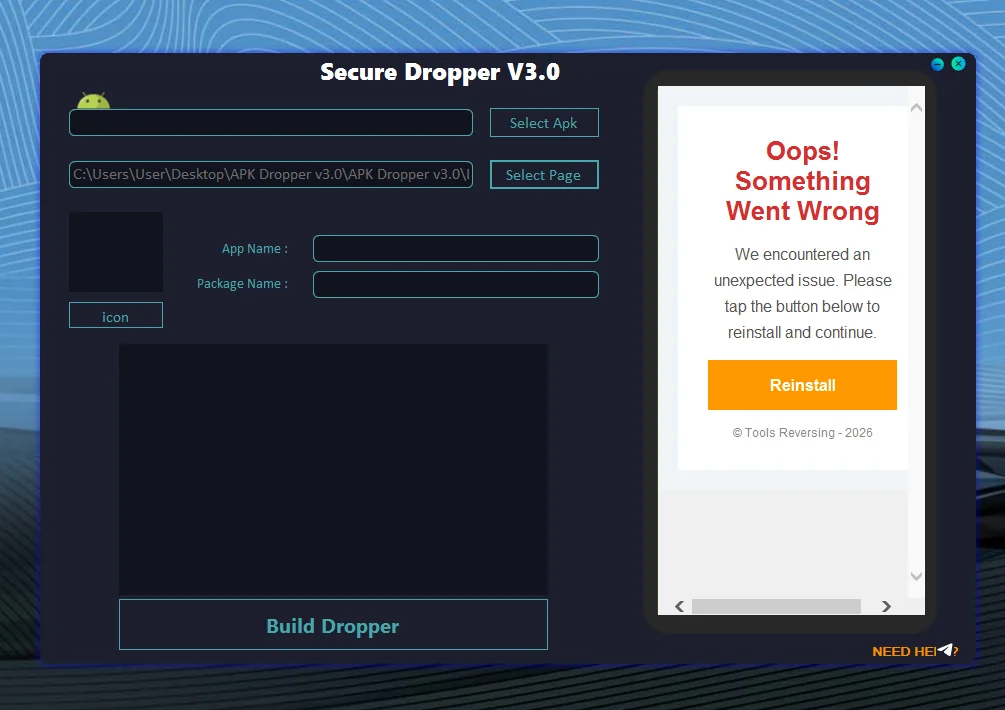
📱 Introduction to APK Dropper v3.0 Malware
Android devices rely on APK (Android Application Package) files to install applications. While most APK files are legitimate, cybercriminals sometimes misuse this format to distribute malicious software.
One of the most common attack techniques is known as a dropper attack. A dropper is a program designed to install or “drop” additional malicious payloads onto a device after the initial application is installed.
Understanding how APK droppers operate is important for developers, security researchers, and Android users who want to protect their devices.
🧩 What Is an APK Dropper v3.0?
An APK Dropper is a type of Android malware that disguises itself as a normal application but secretly installs additional malicious components.
Instead of performing the harmful activity immediately, droppers first bypass detection mechanisms and later deploy the real malware.
⚠ Key Characteristics of APK Dropper v3.0
🔹 Often disguised as legitimate apps
🔹 Installs hidden malware components
🔹 Attempts to bypass mobile security systems
🔹 Frequently used in multi-stage attacks
These techniques allow attackers to distribute malware more effectively.
⚙ How APK Dropper v3.0 Malware Works
Dropper malware usually follows a multi-stage execution process designed to avoid detection.
🪜 Stage 1: Initial Installation
The user installs an application that appears legitimate.
📦 Typical Disguises
✔ Utility applications
✔ Game applications
✔ Modified or unofficial apps
✔ Fake system tools
At this stage, the application may behave normally to avoid suspicion.
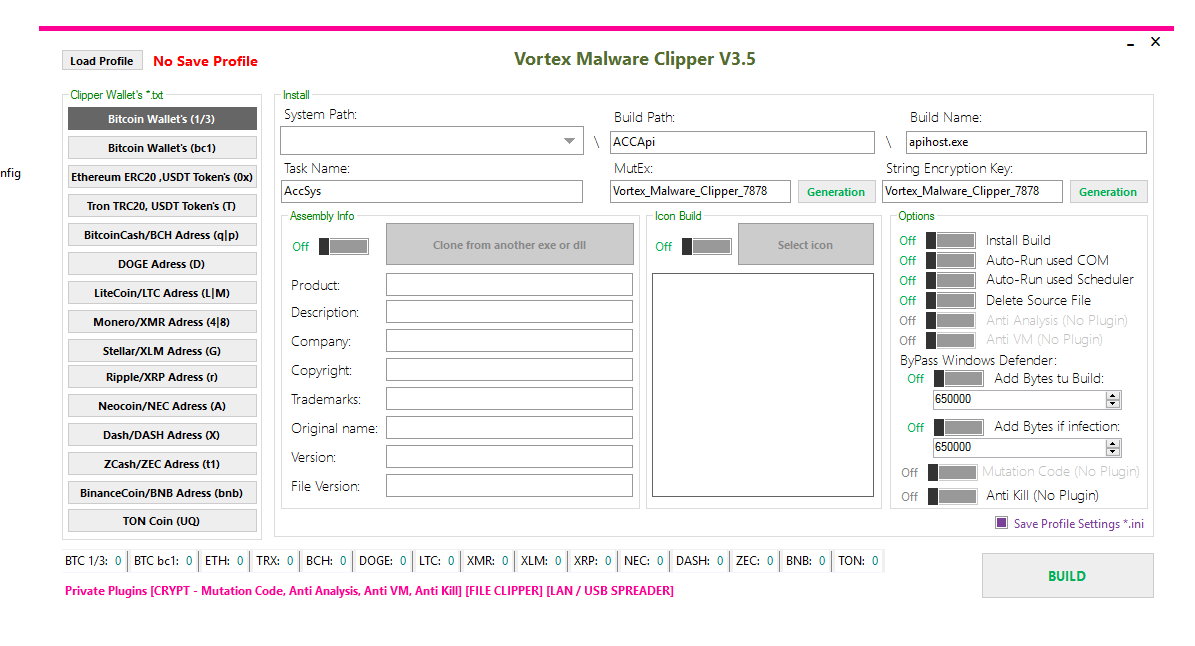
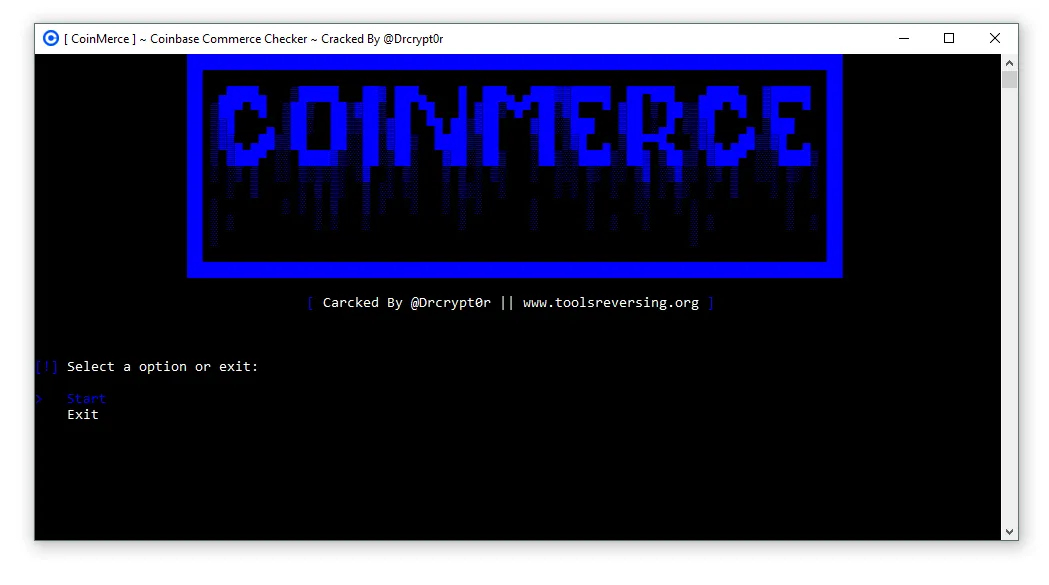
📥 Stage 2: Hidden Payload Delivery
After installation, the dropper secretly downloads or activates additional malicious code.
🔍 Possible Payload Types
🔸 Spyware
🔸 Data-stealing malware
🔸 Banking trojans
🔸 Adware modules
These components may run silently in the background.
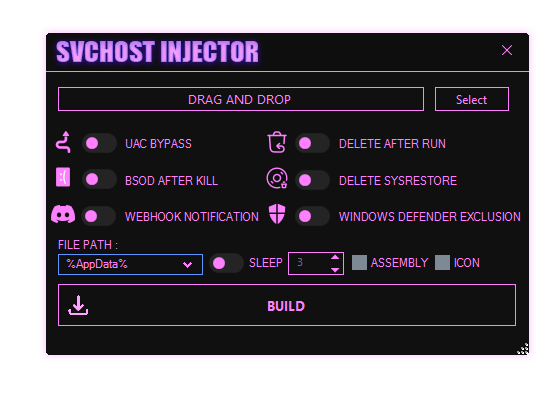
🔐 Stage 3: System Persistence
Once the payload is installed, malware attempts to maintain access to the device.
🛠 Common Persistence Methods
✔ Background services
✔ Hidden processes
✔ Abuse of accessibility permissions
✔ Automatic startup behavior
Persistence allows attackers to maintain control even after device restarts.
🚨 Security Risks Associated With APK Dropper v3.0
Dropper malware can cause serious risks for both individuals and organizations.
⚠ Major Threats
🔴 Theft of personal information
🔴 Banking credential interception
🔴 Unauthorized background activity
🔴 Installation of additional malware
These attacks may lead to privacy breaches, financial loss, or device compromise.
🔍 Why Cybercriminals Use Dropper Techniques
Dropper strategies are popular among attackers because they help avoid detection by mobile security systems.
🧠 Advantages for Attackers
🔹 Malware can be delivered in stages
🔹 Initial app appears harmless
🔹 Security scanners may miss hidden payloads
🔹 Easier to bypass automated analysis
This layered approach makes droppers particularly dangerous.
🛡 How to Protect Android Devices from Dropper Malware
Preventing dropper attacks requires both secure development practices and careful user behavior.
👨💻 Security Practices for Developers
Developers play an important role in protecting the Android ecosystem.
🔐 Recommended Measures
✔ Implement secure code practices
✔ Monitor apps for unauthorized modifications
✔ Protect application integrity
✔ Regularly release security updates
Secure development reduces the risk of malicious app distribution.
📱 Security Tips for Android Users
Users should follow basic precautions to avoid installing harmful applications.
🔎 Safe Mobile Usage Tips
✔ Install apps only from trusted marketplaces
✔ Review application permissions carefully
✔ Keep Android OS updated
✔ Use mobile security tools when needed
These simple habits significantly reduce malware risk.
🧠 Importance of Mobile Malware Awareness
As mobile devices become more powerful, they also become attractive targets for cyber threats.
Understanding threats like APK Dropper v3.0 helps users and organizations:
✔ Recognize suspicious applications
✔ Protect personal data
✔ Strengthen mobile security practices
✔ Improve overall cybersecurity awareness
Education is one of the strongest defenses against modern digital threats.
❓ Frequently Asked Questions (FAQ)
📱 What is an Android dropper?
An Android dropper is a type of malware that installs additional malicious software onto a device after the initial application is installed.
🔍 Are droppers different from normal malware?
Yes. Droppers usually act as delivery mechanisms for other malware rather than performing the main malicious activity themselves.
🛡 Can Android security tools detect droppers?
Modern security solutions can detect many droppers, but attackers constantly modify their techniques to evade detection.
📦 Why are droppers dangerous?
They allow attackers to hide malicious payloads, making them harder for security systems to detect.
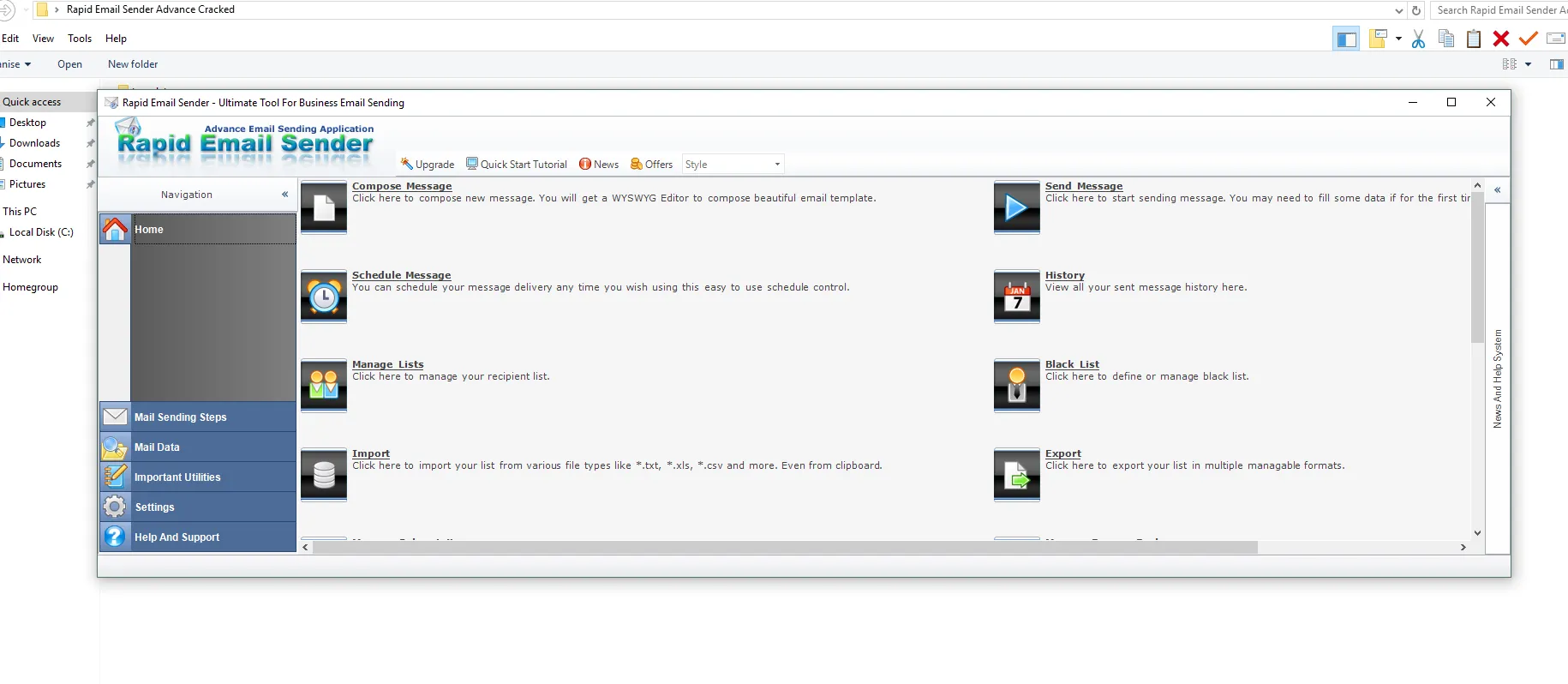
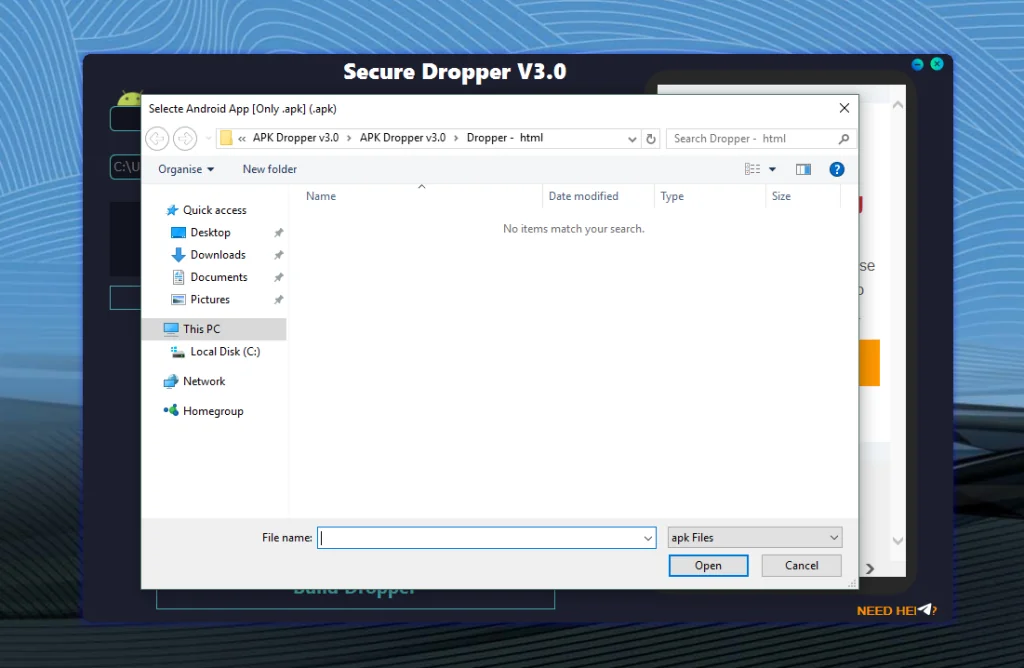
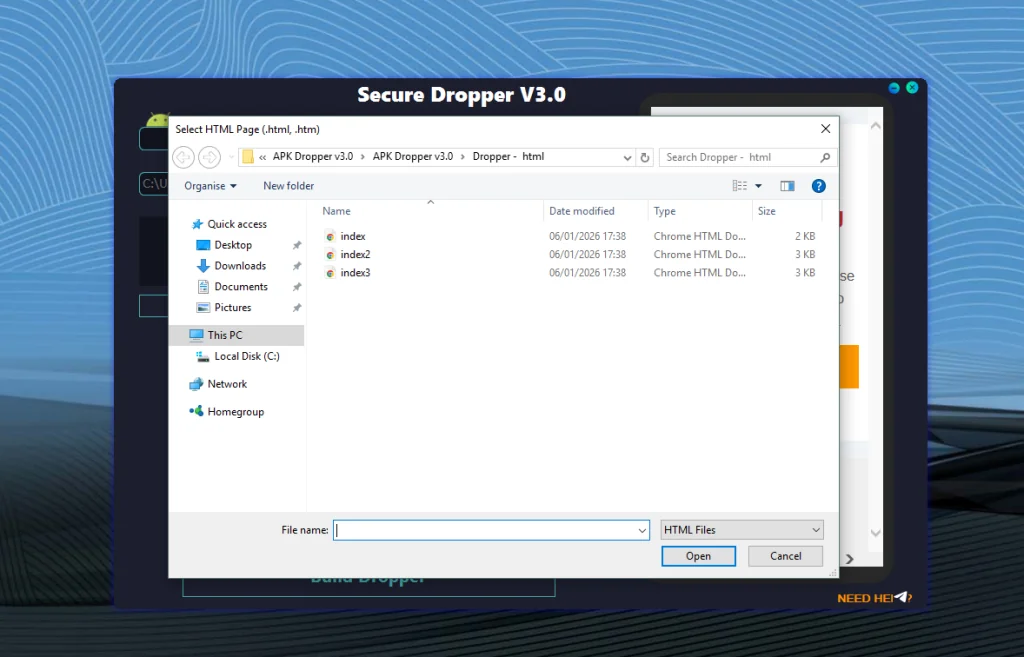
Download APK Dropper v3.0
🏁 Conclusion
APK Dropper v3.0 malware represents a serious threat within the Android ecosystem because it enables attackers to deliver hidden malware in multiple stages.
By understanding how droppers operate and following strong security practices, both developers and users can significantly reduce the risk of mobile compromise.
A proactive approach to mobile cybersecurity awareness remains essential for protecting modern Android devices.