BlueOne V 1.0.1 RAT Cracked
🚀 Introduction
In the world of cyber threats, Remote Access Trojans (RATs) are among the most dangerous malware tools used by attackers. These programs allow hackers to gain complete remote control over infected computers, enabling activities such as surveillance, data theft, and system manipulation.
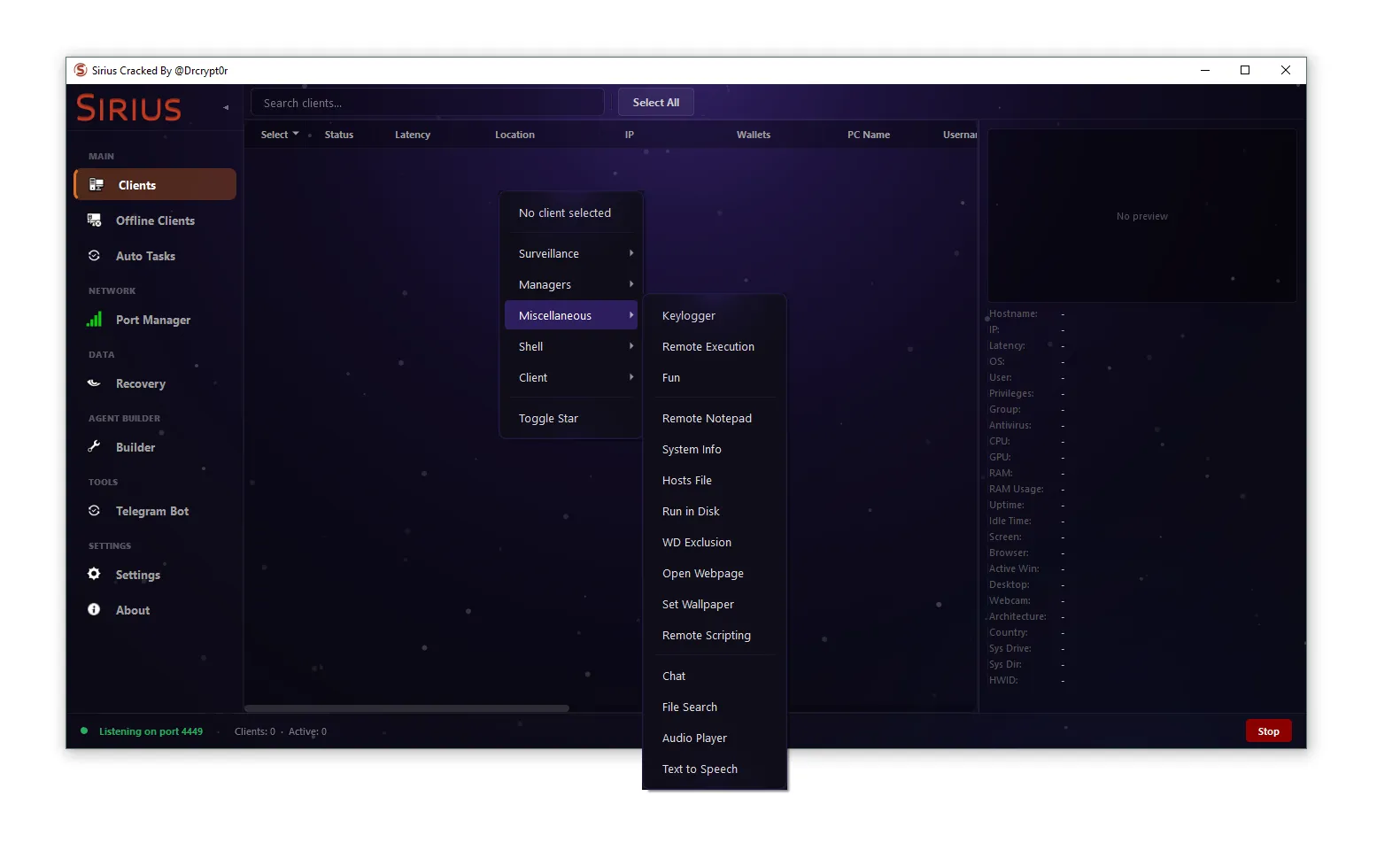
One such tool currently circulating in underground communities is BlueOne V 1.0.1 RAT Cracked
, especially in its cracked and unpacked version. When a RAT is cracked, its original licensing and protection mechanisms are removed, making it freely available to anyone.
This significantly increases the risk of cyberattacks because even inexperienced attackers can use advanced malware tools.
🧠 What is BlueOne V 1.0.1 RAT Cracked?
BlueOne V 1.0.1 RAT Cracked is a remote administration malware designed to give attackers unauthorized access to victim systems.
⚡ Key Characteristics
- 🖥️ Remote system control
- ⌨️ Keylogging functionality
- 🔐 Password recovery modules
- 📂 File management access
- 🎥 Remote desktop monitoring
- 🕵️ Hidden Virtual Network Computing (HVNC)
The cracked version labeled “Cracked & Unpacked” indicates that the original protection mechanisms have been removed.
⚙️ BlueOne V 1.0.1 RAT Cracked Architecture
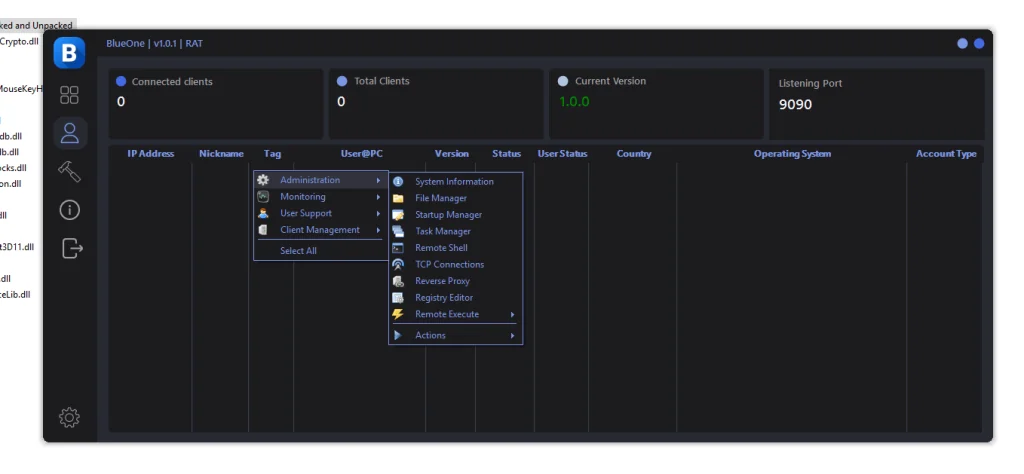
Like most RAT malware, BlueOne uses a client-server architecture.
🧩 Core Components
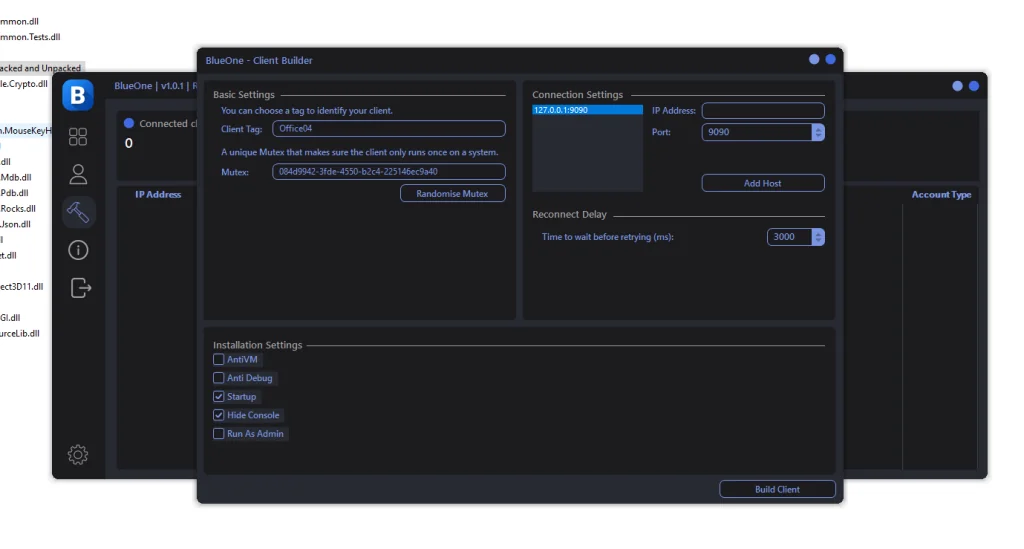
🛠️ Builder (Client Generator)
The builder allows attackers to create customized malware payloads.
Features include:
- ⚙️ Host configuration
- 🔑 Mutex generation
- 🧬 Anti-analysis settings
- 📦 Payload compilation
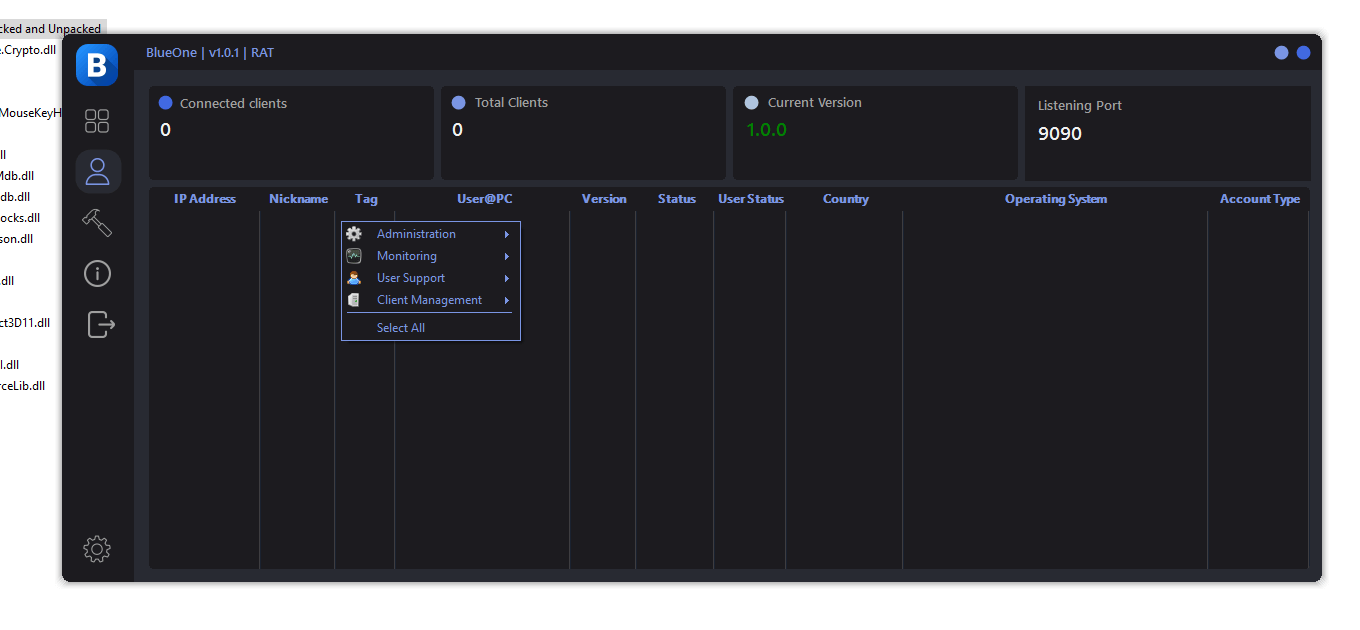
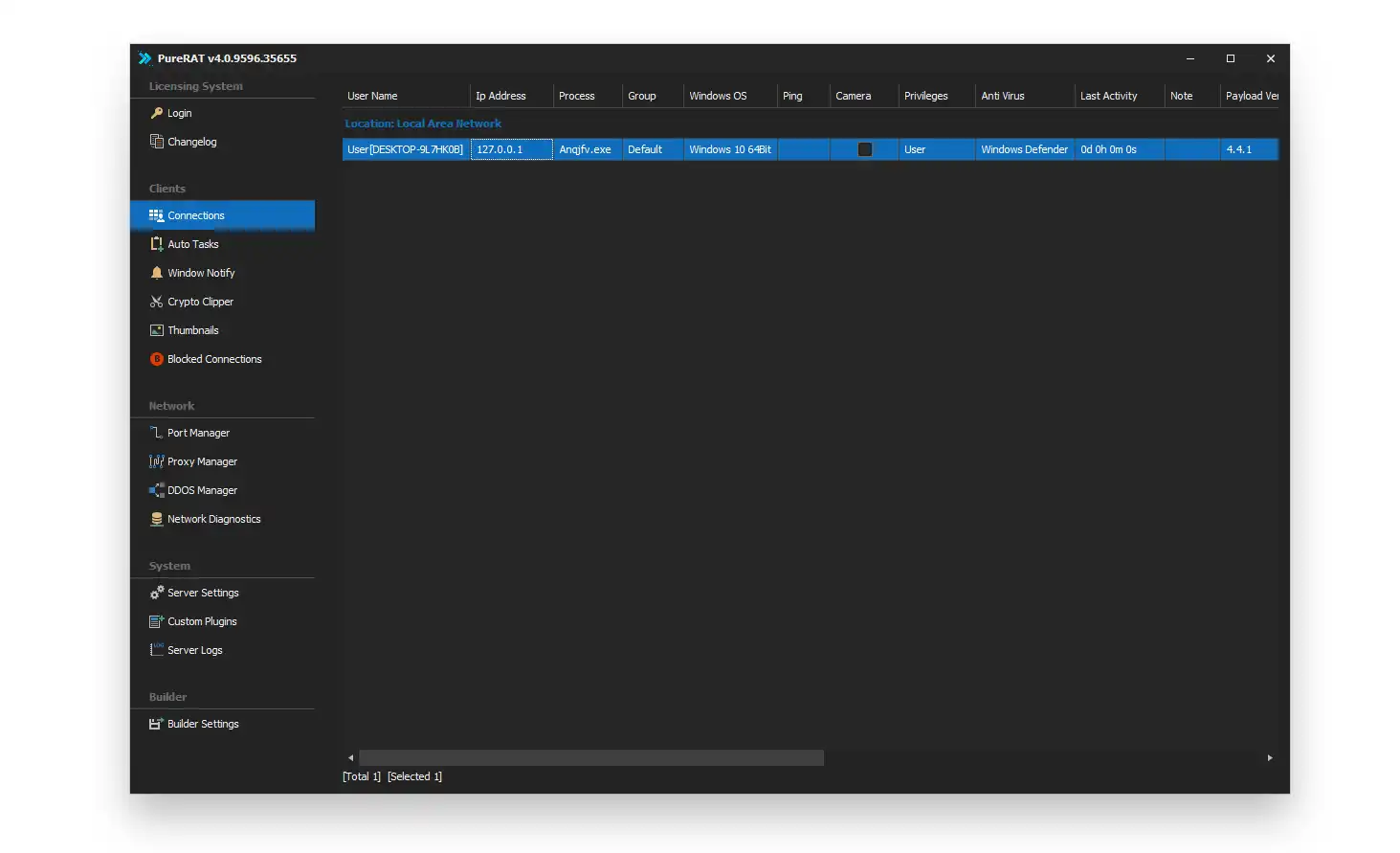
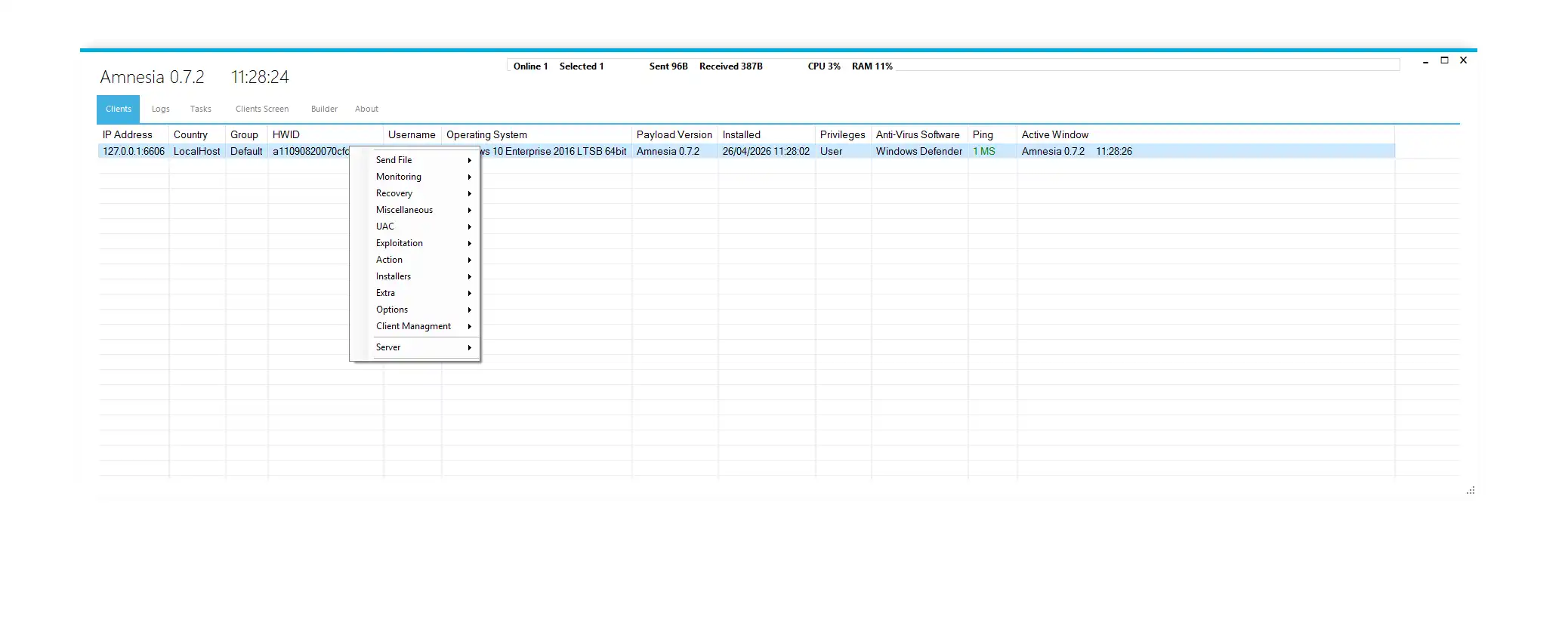
🖥️ Command & Control Panel (C2)
The control panel acts as the attacker dashboard where infected systems are monitored.
Displayed information may include:
- 🌍 Victim IP address
- 💻 Operating system
- 👤 Username and PC name
- 📍 Country location
- 📡 Connection status
🎯 Victim Client
This is the malicious program installed on the victim’s computer.
It connects to the command server and executes commands sent by the attacker.
🛠️ Builder Configuration Options
Attackers can customize malware behavior using the builder interface.
🔧 Basic Configuration
- 🏷️ Client Tag: Used to identify infected systems
- 🔑 Mutex Value: Prevents multiple malware instances
- 🌐 Host Address: C2 server address
- 🔌 Default Port: 9090
- ⏱️ Reconnect Delay: 3000 milliseconds
These settings ensure stable communication between the infected system and the attacker.
🛡️ Evasion & Persistence Mechanisms
To avoid detection, BlueOne V 1.0.1 RAT Cracked includes several anti-analysis features.
🧪 Anti Virtual Machine
The malware can detect virtual environments such as:
- VMware
- VirtualBox
- Hyper-V
If detected, the malware may stop execution to avoid analysis.
🐞 Anti-Debug Protection
BlueOne V 1.0.1 RAT Cracked may attempt to detect debugging tools including:
- x64dbg
- OllyDbg
- WinDbg
- IDA Pro
This prevents security researchers from analyzing the malware easily.
🔁 Persistence Methods
To remain active after reboot, the malware may use:
- 🗂️ Windows startup registry entries
- 📁 Startup folder installation
- ⏰ Scheduled tasks
- 🔗 DLL side-loading
📊 BlueOne V 1.0.1 RAT Cracked Control Panel Features
The control panel allows attackers to manage infected systems.
📋 Main Dashboard Data
- 🌍 Victim IP address
- 🖥️ Operating system
- 👤 User account
- 📡 Online status
- 🏳️ Country location
- 🔐 Privilege level
Attackers can organize infected systems into groups for easier management.
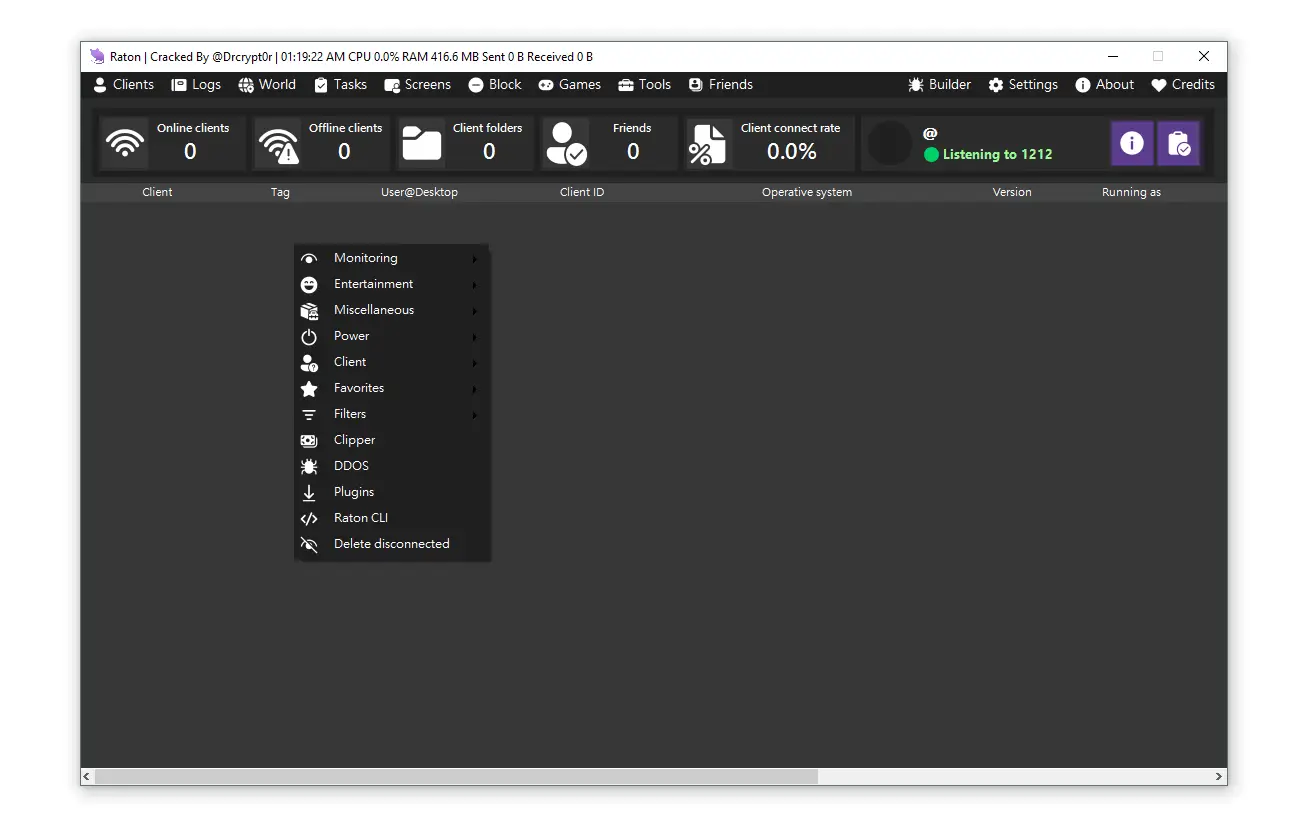
🧰 Remote Administration Capabilities
BlueOne V 1.0.1 RAT Cracked provides numerous malicious features.
📂 File Manager
Attackers can:
- 📁 Browse files
- ⬇️ Download files
- ⬆️ Upload malware
- ❌ Delete data
- ▶️ Execute programs
🧠 System Information Gathering
BlueOne V 1.0.1 RAT Cracked can collect information such as:
- CPU and RAM details
- Installed software
- Network configuration
- Security software status
🖥️ Remote Shell
Attackers can execute commands using:
- Windows CMD
- PowerShell
- Scripts or executables
This provides complete control of the infected system.
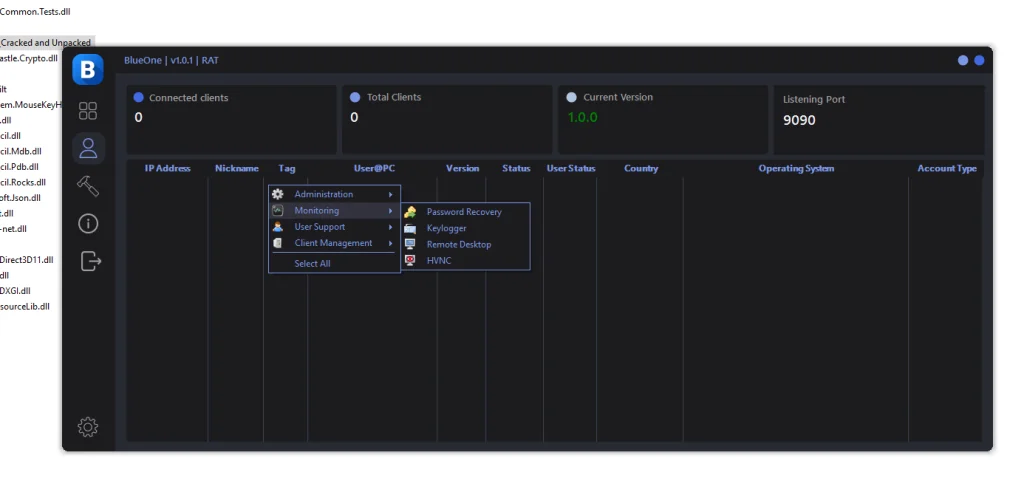
🔐 Credential Theft Features
One of the most dangerous aspects of RAT malware is its ability to steal credentials.
🔑 Password Recovery
Targets include:
- 🌐 Web browsers
- 📧 Email clients
- 📂 FTP software
- 🔒 VPN credentials
- 📶 WiFi passwords
⌨️ Keylogger
The keylogging module records all keyboard activity including:
- Login credentials
- Banking information
- Private conversations
- Sensitive documents
🕵️ HVNC – Hidden Remote Desktop
One of the most advanced features is Hidden Virtual Network Computing (HVNC).
⚡ HVNC Capabilities
- 👁️ Invisible desktop session
- 🖱️ Remote interaction without victim awareness
- 💳 Used in banking fraud attacks
- 🕶️ Completely hidden from the user
📦 DLL Components Observed
The unpacked malware contains several DLL files.
📚 Possible Components
- DirectX related libraries for screen capture
- Core malware functionality libraries
- Encryption modules for secure communication
These modules allow the RAT to perform its operations while avoiding detection.
⚠️ Security Risks of Cracked RATs
The distribution of cracked malware significantly increases cyber risks.
🚨 Major Concerns
- 📉 Free access for inexperienced attackers
- 🌍 Increased global cyber attacks
- 🧬 Malware modifications and backdoors
- 🧠 Harder threat attribution for security researchers
🔎 Indicators of Compromise (IoCs)
Security teams should monitor systems for suspicious activity.
🌐 Network Indicators
- Connections to unknown servers
- Traffic on port 9090
- Repeated connection attempts
📂 File Indicators
Suspicious files may appear in:
- AppData folders
- Temporary directories
- Startup folders
🗂️ Registry Indicators
Malware persistence entries may appear in:
HKCU\Software\Microsoft\Windows\CurrentVersion\Run
🛡️ Protection & Mitigation Strategies
👤 For Individuals
- 🛡️ Install trusted antivirus software
- 📥 Avoid suspicious downloads
- 🔄 Keep systems updated
- 🔐 Use strong passwords
- 📲 Enable multi-factor authentication
🏢 For Organizations
- 🧠 Deploy Endpoint Detection & Response (EDR)
- 🌐 Monitor network traffic
- 🚫 Implement application whitelisting
- 🎓 Conduct cybersecurity training
- 💾 Maintain secure backups
⬇️ Download BlueOne RAT v1.0.1
⚠️ Disclaimer: Provided strictly for cybersecurity research and malware analysis.
🔗 Download Links
❓ FAQ – BlueOne RAT
❓ What is BlueOne V 1.0.1 RAT Cracked?
BlueOne RAT v1.0.1 is a remote access trojan that allows attackers to remotely control infected computers, steal data, and monitor users.
❓ What does “Cracked Version” mean?
A cracked version means the original licensing protection has been removed, allowing the malware to be distributed freely.
❓ What is HVNC in BlueOne RAT?
HVNC (Hidden Virtual Network Computing) creates an invisible desktop session allowing attackers to control a system without the user noticing.
❓ How can BlueOne RAT be detected?
Detection may involve monitoring unusual network traffic, suspicious startup entries, or unknown processes running on the system.